The “agentless, low-code” pitch often wins the first six months, but many teams hit a Complexity Tax by year two. That tax shows up as YAML sprawl, brittle automation and increasing maintenance time as environments grow.
Progress Chef takes a different approach: Policy-as-Code with Chef and an agent driven Pull architecture.
A Practical Model for Automation ROI
To evaluate automation platforms, focus on Realized Value (RV) not just license cost:
Inputs:
- Emanual : Effort (hours) for manual configuration/drift correction
- Eauto : Effort (hours) using the tool (authoring, runs, fixes)
- Clabor : Hourly cost of engineering talent
- Clicensing : Tool licensing/platform cost
- Cupdates : Hours spent on upgrades/updates (near‑zero with Chef SaaS)
Realized Value (annual):
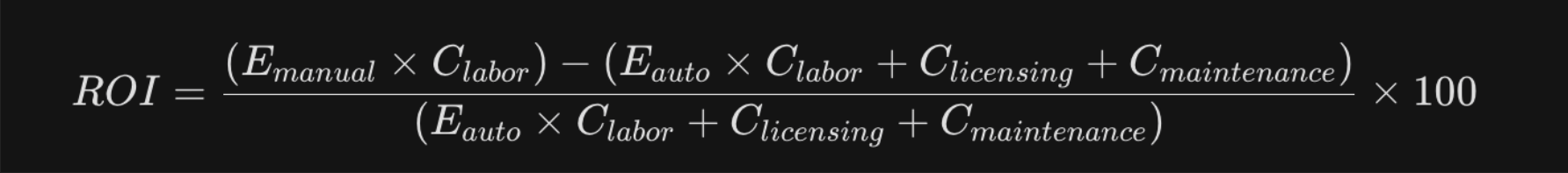
At scale, push-based‑ YAML workflows (e.g., Ansible) typically see 𝐸𝑎𝑢𝑡𝑜 rise over time due to SSH fan‑out bottlenecks and “when/filter/tag” complexity. The Chef pull model + Ruby DSL tends to keep 𝐸𝑎𝑢𝑡𝑜 low, thanks to drift correction, code reuse, and powerful abstraction.
The result is measurable outcomes at enterprise scale (Example: 5,000+ nodes):
227% three‑year ROI, driven by sustained reduction in manual configuration effort and drift remediation labour, measured against total automation cost (engineering time, licensing, and maintenance)
~40 engineer hours/month in toil eliminated per person
Significantly reduces audit preparation effort by embedding compliance checks directly into the infrastructure workflow
Reduced code duplication through reusable abstractions and custom resources
Chef turns infrastructure from scripts into software testable, composable and resilient so teams can scale without drowning in duplication.
Why Chef Wins: Four Pillars of ROI and Maintainability
1) Eliminate the “YAML Tax” with Real Programming Constructs
YAML-based tools are optimized for declarative configuration, but expressing complex, state-dependent logic often requires layering templates, conditionals and modular structures, which can become difficult to maintain at scale.
The Chefs Policy as Code approach gives you native programmatic capabilities (conditionals, iteration, modules and custom resources). You write less code that does more and you can test it like software.
Same intent, different complexity:
Ansible (YAML sprawl):
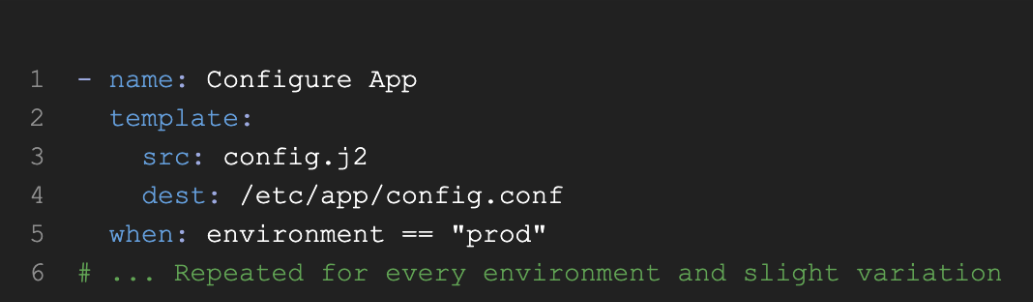
Chef (Policy as Code, elegant):
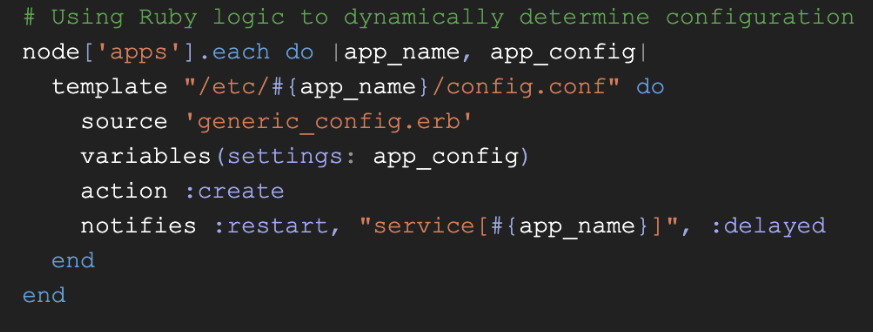
Value Insight: One recipe can cover thousands of permutations. Teams commonly see ~60% fewer LoC compared to YAML patterns, leading to fewer bugs and faster audits.
2) The Power of the Pull Architecture (Agent = Feature)
The pull‑based architecture of Chefreverses the traditional “central push” model. Instead of a control node connecting to thousands of systems and executing changes remotely, each node runs a lightweight agent that continuously pulls the desired state and converges locally. This shifts complexity away from the control plane and turns the agent into a reliability and scale advantage, not an operational burden.
Drift Correction: Chef clients converge on a defined schedule (for example, every 30 minutes). Any manual or accidental configuration changes are automatically corrected back to the declared policy, without waiting for a centralized run.
Scale: Nodes pull instructions independently, so the control plane is not coordinating thousands of SSH sessions or parallel executions. This makes fleet growth predictable and stable even at very large node counts.
Resilience: Transient network or control-plane issues do not derail global operations. Nodes reconcile themselves once connectivity is restored, rather than failing an entire run.
Flexibility: While the agent-driven pull model is ideal for long‑lived infrastructure, Chef also supports agentless and on‑demand execution patterns for ephemeral nodes, edge cases, and environments where installing an agent is not practical—allowing teams to choose the right execution model per use case.
3) Integrated Compliance
Compliance-as-Code is native to Chef. Teams can define, version and run security controls alongside infrastructure policy. Organizations report up to 90% less audit prep time because what runs and what’s proven live in one pipeline.
4) Don't Repeat Yourself by Design: Abstraction with Custom Resources
Senior architects encode the complex “how” once; teams consume a simple “what” interface everywhere.
Chef Custom Resource (encapsulating complexity):
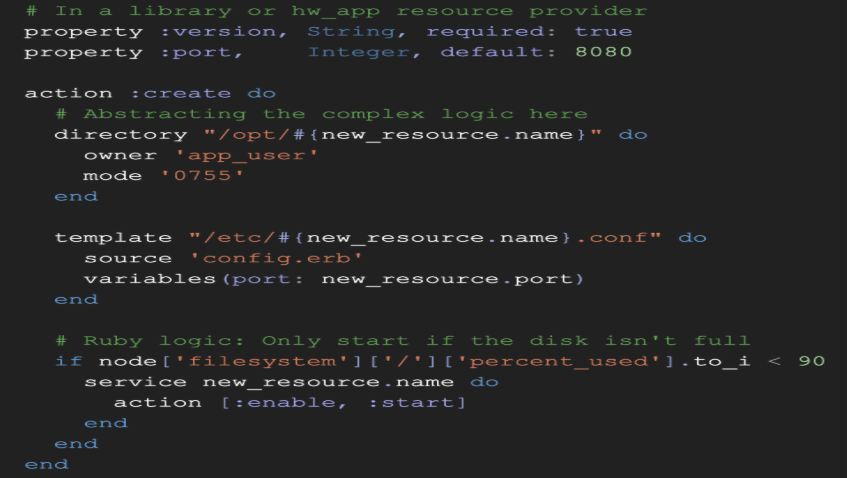
Usage (what teams write):
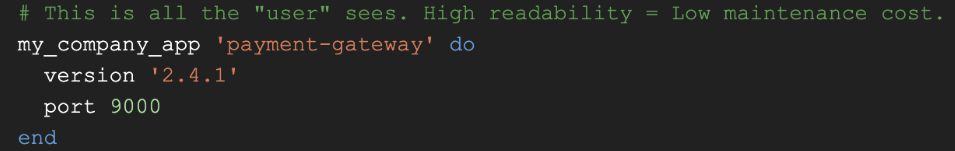
Value Insight: Replace 200-line YAML flows with a single, safe block. Junior engineers ship reliably; senior engineers eliminate duplication and drift-prone “hacks.”
Real-World Example: Multi-Environment Application Deployment
In a typical enterprise setup, deploying an application across environments (dev, staging, prod) requires:
- Environment-specific configs
- Conditional logic (feature flags, ports, endpoints)
- Secrets handling
- Service orchestration
YAML-based approach often results in:
- Multiple playbooks per environment
- Repeated conditional blocks
- Increased maintenance overhead
Chef approach: A single custom resource encapsulates:
- Environment-aware configuration
- Secret injection
- Service lifecycle management
Example usage:
customer_app 'payments-service' do
environment 'prod'
enable_audit true
secrets data_bag_item('secrets', 'payments')
end Outcome:
- One interface replaces multiple playbooks
- Logic is centralized and testable
- Changes propagate consistently across environments
Comparison at a Glance
Area | Ansible (YAML + Push) | Chef (Policy as Code + Pull) |
Scale | Push-based models rely on centralized orchestration, which can introduce coordination complexity and execution overhead as fleet size and concurrency requirements grow. | Agent pull scales to very large fleets |
Drift Handling | Manual remediation or episodic re‑runs | Periodic auto-convergence (self-healing) |
Compliance | Typically, addon tools | Built‑in InSpec (Compliance‑as‑Code) |
Maintainability | YAML sprawl over time | Reuse, inheritance, testability |
TCO Trendline | Grows with Complexity | Stays low via reuse and policy |
Execution Model | Centralized execution (control node driven) | Distributed execution (node-driven convergence) |
Resilience | Failures during execution may require reruns or manual intervention | Nodes reconcile state independently after transient failures |
Observability | Execution logs are centralized per run but require correlation across systems | Integrated visibility across node state, runs, and compliance |
Performance at Scale | SSH fan-out and orchestration overhead can increase with large parallel operations | Distributed execution minimizes central bottlenecks |
Implementation Roadmap
Phase 0: Baseline and Business Case
Measure toil: manual patching hours, config drift incidents, time-to-fix.
Identify “YAML clones”: repeated playbook blocks and brittle condition chains.
Phase 1: Establish a Thin “Base” Cookbook
Create a Base cookbook for security baselines, users, and monitoring across all nodes.
Start using Policyfiles so what you test is what you run (Dev = Prod).
Phase 2: Encapsulate Complexity
Build 1–3 Custom Resources to replace multi‑step YAML deployments (apps, agents, config packs).
Migrate early adopter services to these resources to demonstrate DRY wins.
Phase 3: Test and Integrate Compliance
Add ChefSpec unit tests and Test Kitchen scenarios for repeatable validation.
Run InSpec profiles alongside Infra recipes to keep every change secure by design.
Phase 4: Scale and Sunset Legacy
Expand to top services/workloads; deprecate brittle scripts.
Track KPIs: toil hours ↓, drift incidents ↓, audit prep time ↓, delivery velocity ↑.
Conclusion
At enterprise scale, infrastructure automation is no longer about speed; it is about reliability, risk reduction, and predictable cost. YAML‑centric tools struggle as logic grows dynamic, leading to duplication, brittle conditionals, and long‑term operational sprawl.
A Policy‑as‑Code approach treats infrastructure as real software programmable, testable, and reusable so automation improves as it scales. This is why Chef delivers lower TCO and higher operational confidence: it is not just an automation tool, but an operating model for modern infrastructure.
The move from YAML‑driven configuration to true Policy‑as‑Code engineering is the difference between temporary automation and durable operational excellence.
Are your engineers scaling systems or just maintaining scripts?
Progress Chef helps teams move from YAML editing to true infrastructure engineering, turning automation into a durable internal platform.
Ready to move beyond YAML sprawl?
Explore how Progress Chef 360 can transform your infrastructure into scalable, testable Policy-as-Code.


