Infrastructure Management
Automate, Scale and Integrate DevSecOps Into Infrastructure Management
Apply configurations consistently across environments and manage your infrastructure with ease using the Chef Automation Platform.
Request a DemoChef in 60 seconds
Using Chef, You Can:
Change Safely
Automate systems' adherence to declared desired state and minimize security delays and fire drills.
Scale Easily
The largest companies in the world, like Meta, GM and SAP count on Chef to automate infrastructure management at a massive scale.
Run Anywhere
Infrastructure automation solutions for multi-OS, multi-cloud, on-premises, agentless, hybrid and complex legacy architectures.
Leverage Insights
Real-time data that is easy to filter and provides reachable and actionable data for every node under management.
Core Features
Unlock Infrastructure Efficiency
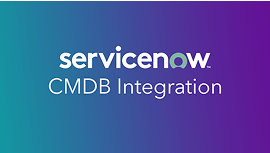
Available Languages
Automation is only as complex as the problems it needs to solve; use a human readable language and a Ruby model when faced with complex scenarios.
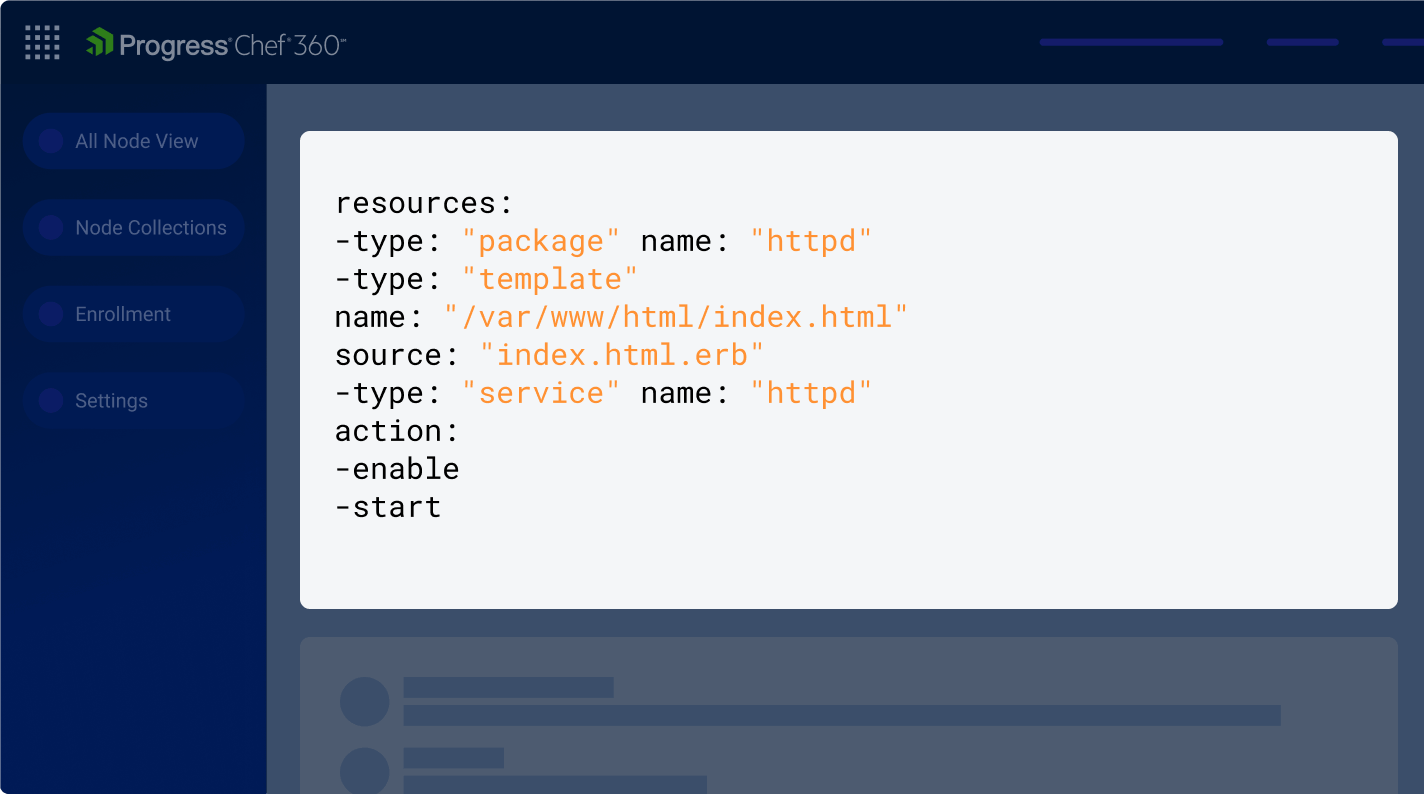
Access Control
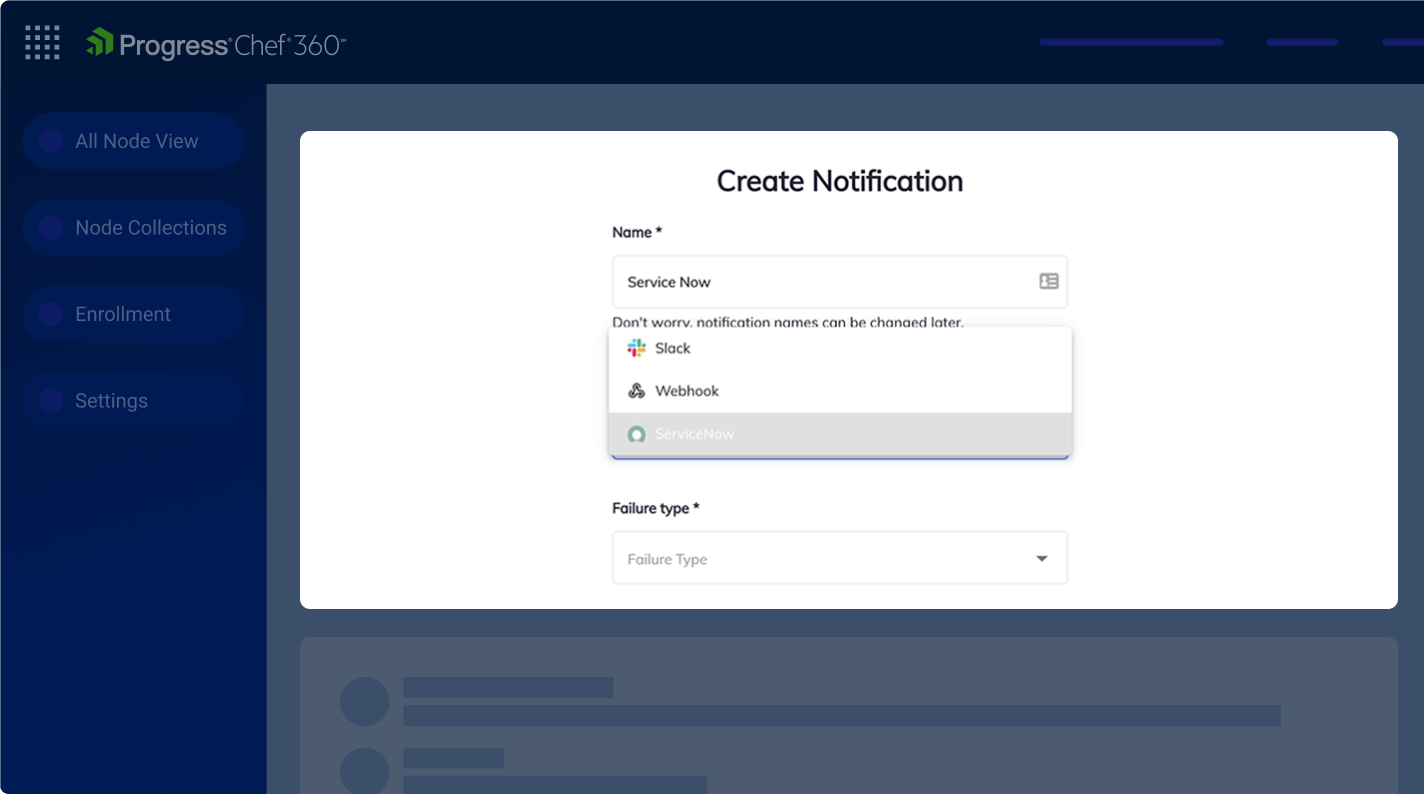
Customize and provide resource-specific authorizations to users and teams. Notifications can be displayed on a per-node or per-failure basis.
Testing Environment
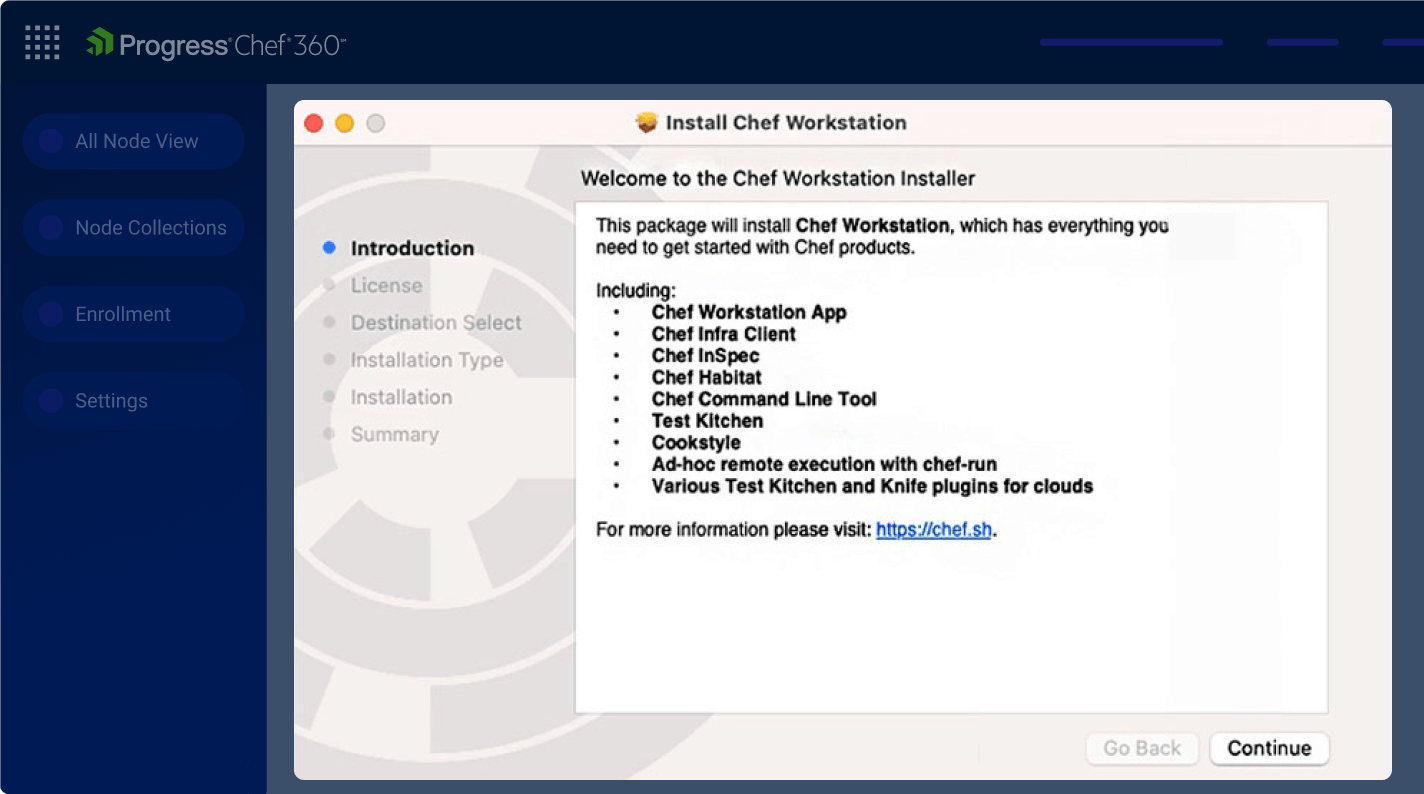
The Chef platform includes Workstation - a development toolkit designed to streamline creation, testing and deploying configurations and policies efficiently.
AIOps Data Mapping
With a multitude of supporting integrations to leverage, data can be sent to intelligence and monitoring systems via a feature called 'Data Path' (including an advanced 2-way integration with ServiceNow CMDB and webhook notifications).
Unlock Infrastructure Efficiency
Integrate with various software across the DevOps ecosystem, including source code and artefact repositories, CI/CD pipelines, provisioning software and secrets management tools.

Latest from Chef
Automation Tools Use Cases
Consistent Configuration
Eliminate configuration drift and continuously enforce desired state.
Hybrid Cloud Control
Effectively work with different clouds minimizing complexity through multi-cloud support.
System Hardening
Reduce risks by ensuring OSs, firmware, and system libraries are kept up to date.
Continuous Delivery Pipeline Automation
Enable developer services and drive pull-based CI/CD system workflows.
High Security, Low Trust Environments
Control access and accelerate delivery in highly regulated environments.
Automated Remediation
Event-driven automation that can immediately correct configuration drift.
Principle of Infrastructure Automation with Chef
Bridge the gap between configuration and compliance with an as-code approach while having complete visibility over your IT fleet.
Infrastructure as Code
Use Infrastructure as Code to automate infrastructure management across Windows, Linux and MacOS and more.
Single Pane of Glass
Maintain consistency across clouds with a GUI-based control plane that works in real-time and on-demand.
Configuration Meets Compliance
Use a single agent for configuration and compliance.
People Proven Progress
Discover how the Chef platform helps drive success for teams and organizations.
-
Continuous Compliance and Streamlined Auditing
Use the Chef platform not just for configuration management but for security and compliance checks too.
-
Policy as Code
Convert policy documents into Chef policies easily with code and automate both misconfiguration detection and remediation.
-
Job Orchestration at Scale
Automate complex, condition based actions like patching, update rollouts or maintenance across large fleets of servers.