Compliance Management
Automate, Scale and Codify Compliance Into Every Workflow
Embed policies as code, detect misconfigurations early and meet audit standards—without disrupting delivery.
Request Free Trial Talk to an ExpertCompliance Automation with Progress Chef
Unlock Continuous Compliance at Scale
The Progress® Chef® solution helps teams turn policy goals into continuous, testable and automated enforcement. Here's how you can apply it:
Codify Compliance as Code
Write human-readable rules that are version-controlled, reusable and testable - no more scattered spreadsheets or ad hoc checklists.
Shift Compliance Left
Catch configuration violations early in the development lifecycle, before they ever reach production.
Audit Anything, Anywhere
Run compliance scans across bare metal, VMs, cloud accounts, containers and even air-gapped environments.
Automate Remediation
Connect findings to actions. Automatically fix issues at the source instead of waiting for post-incident recovery.
Policy Enforcement Starts with a Shared Language
Security, DevOps, and compliance teams often speak different operational languages, which leads to silos, friction and audit delays. The Chef solution bridges this gap by turning compliance rules into executable, version-controlled code that everyone can work with. The Chef platform enables you to:
- Validate system state continuously
- Create reusable controls in YAML
- Scan anything - Linux, Windows, macOS, containers, clouds, endpoints
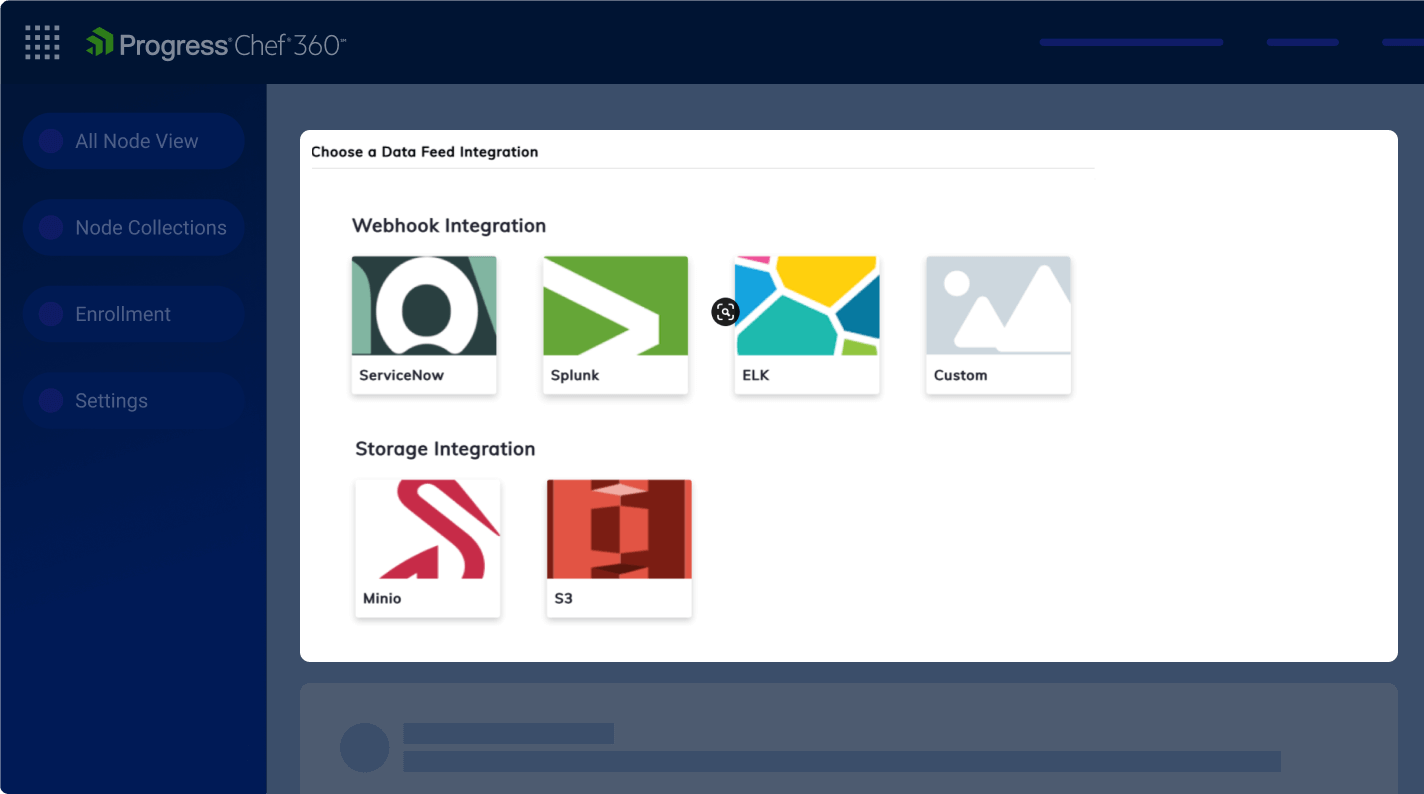
- Integrate directly into pipelines and audit systems

Explore AI Capabilities in the Chef 360 Platform
From Prompt to Production, Legacy Cookbook Modernization, with AI Detection to Remediation on One Platform Built for Operations Teams
Core Features
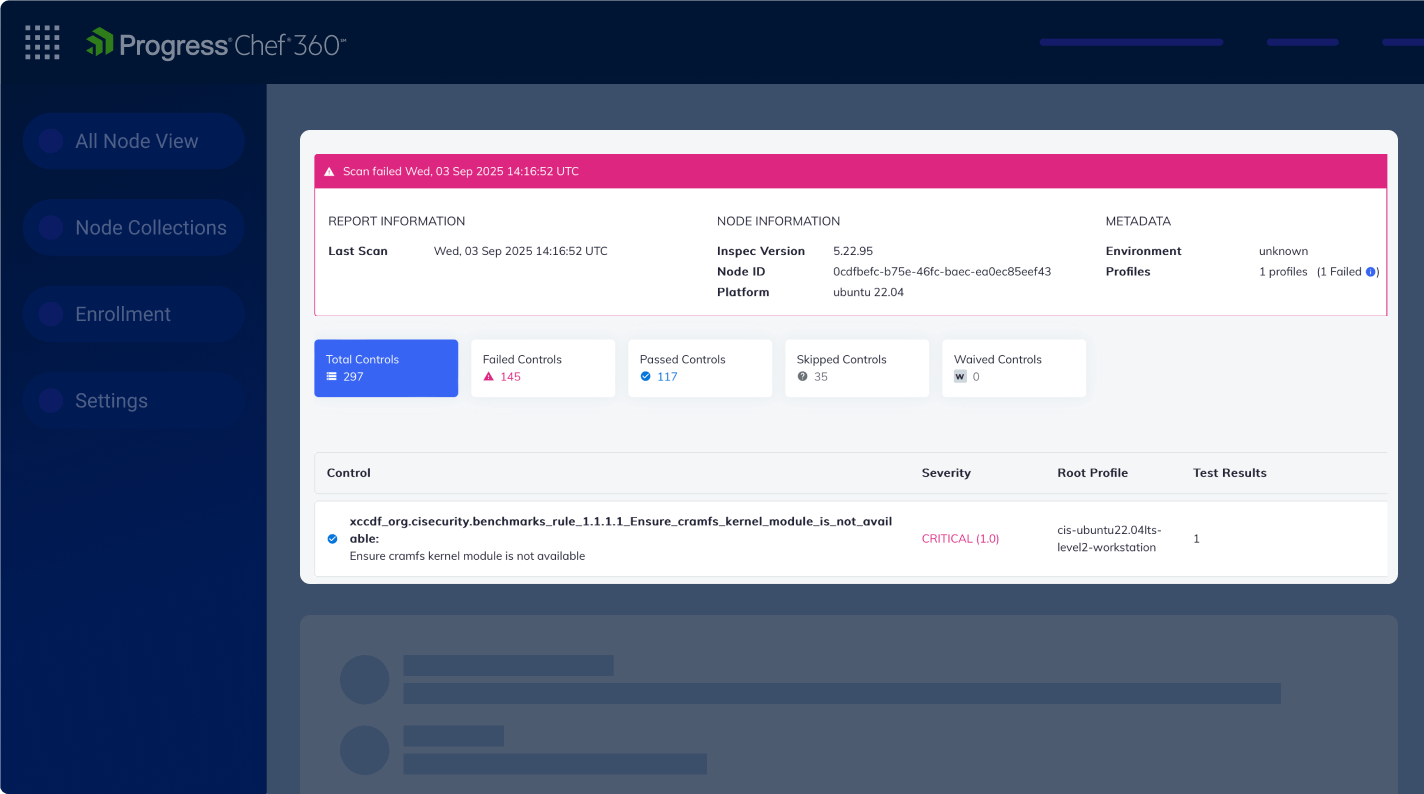
Chef Compliance Management in Practice
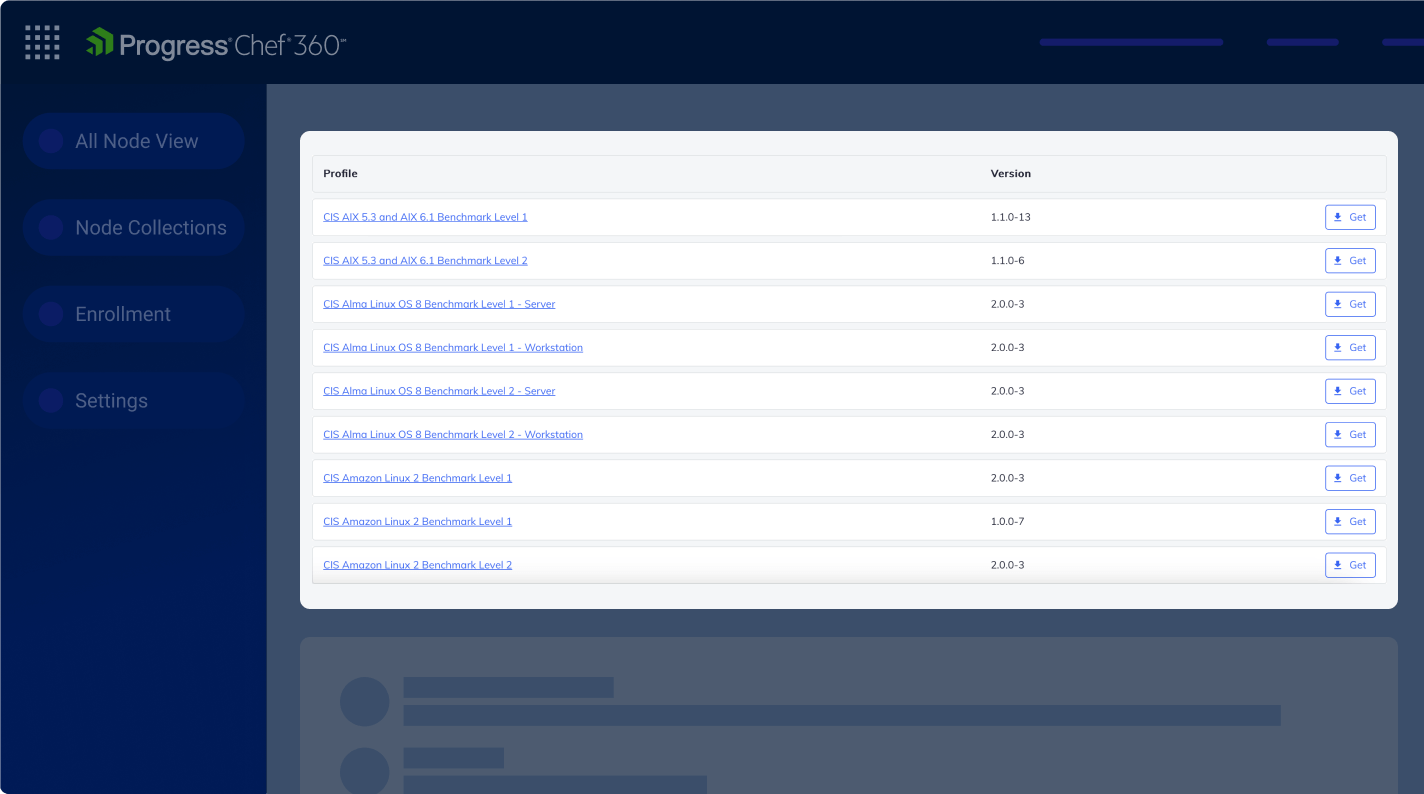
Premium Content
Access prebuilt, customizable security and compliance profiles—like CIS benchmarks, DISA STIGs, and Chef-curated guides.
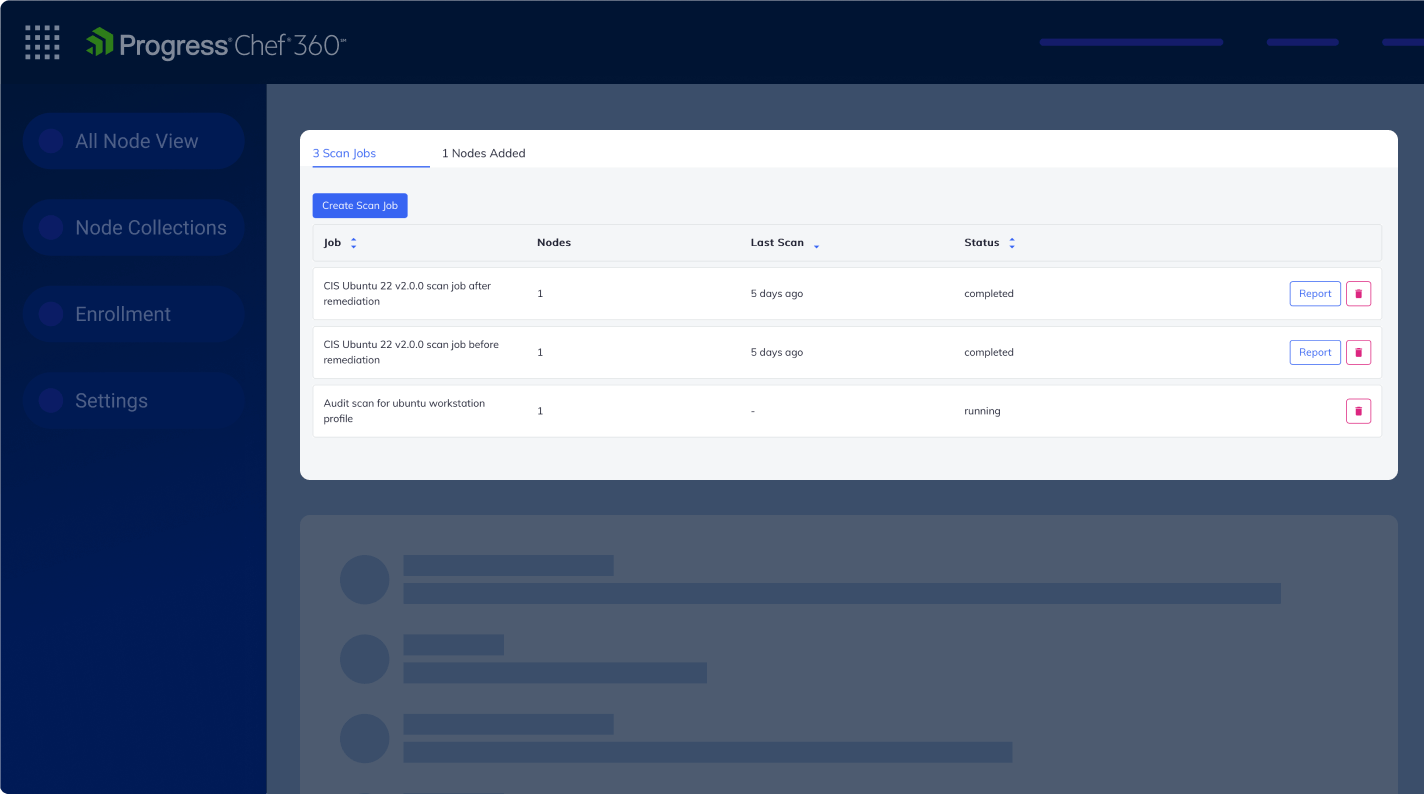
Automated Scans
Define scan targets for Linux, Windows, containers, cloud accounts (AWS, Azure, GCP) and even offline/air-gapped nodes.
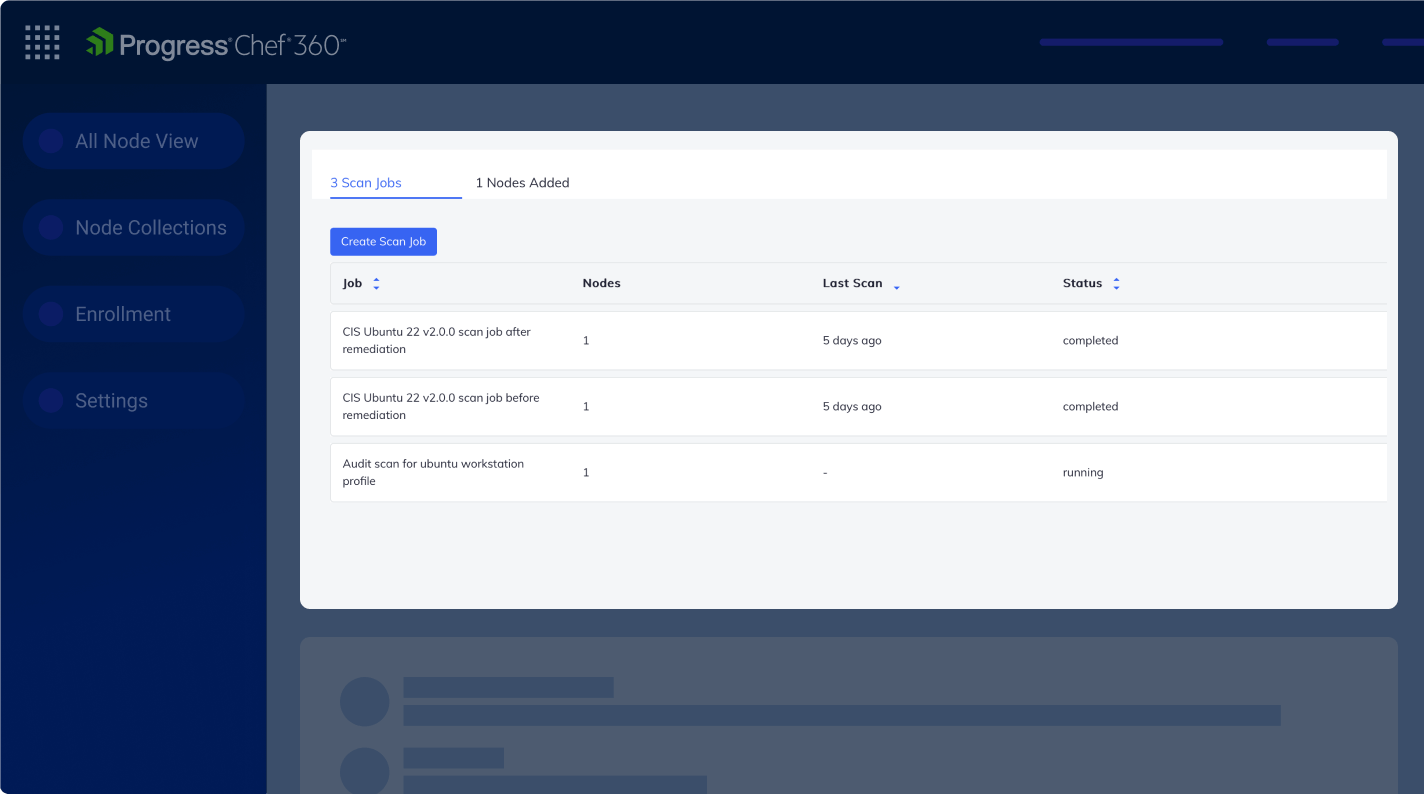
Automate Scans with Scheduled or Event-Driven Triggers
Run compliance scans periodically or trigger on demand by changes in GitHub, Jenkins or infrastructure.
Integrated CI/CD
Embed compliance checks into your CI tools to fail builds on policy violations and maintain secure delivery pipelines.
Automated Remediation
Link failed controls to fixes via Chef Infra Cookbooks or remediation scripts; apply manually or auto-trigger to close the detection-correction loop.
Unified Fleet View
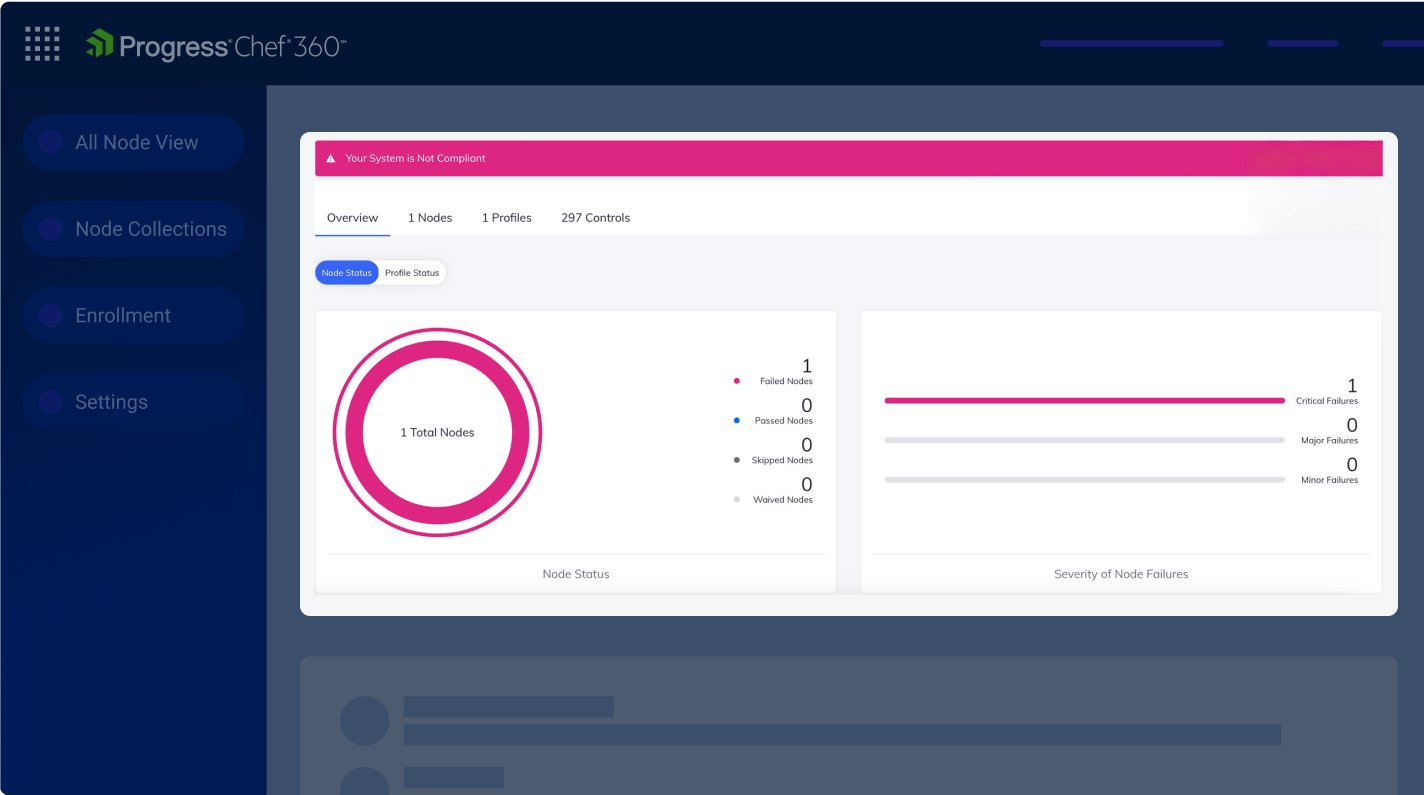
Get a centralized, real-time dashboard built to track drift and monitor remediation and policy adherence across your entire fleet.
Latest from Chef
Use Cases
Enforce Security and Compliance Baselines Across Teams
Standardize control sets using reusable policies to maintain org-wide consistency.
Accelerate Audit Readiness
Generate audit-ready reports that map directly to frameworks like CIS, PCI, HIPAA, and DORA.
Validate Policies Early in CI/CD
Catch and help prevent misconfigurations at the source by embedding compliance checks directly into your pipelines.
Apply Zero Trust at the Configuration Layer
Treat every node as untrusted and enforce hardened configurations everywhere.
Tailor Policies to Internal Requirements
Customize controls, waivers and exceptions to align with internal governance needs.
Extend Compliance to Cloud Infrastructure
Apply codified controls across AWS, Azure, and GCP to audit cloud resources, enforce security baselines and maintain continuous visibility across hybrid environments.