Chef Automate provides DevOps teams a dashboard for complete operational visibility across large-scale or mission-critical infrastructure. This comprehensive visibility allows developers, operators, and security engineers to collaborate on delivering application and infrastructure changes at the speed of business. Chef Automate provides real-time data across the estate with intelligent access controls, ensuring the right team has the right access.
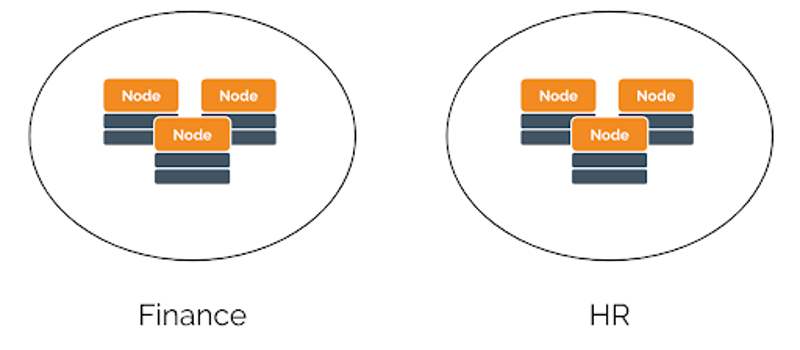
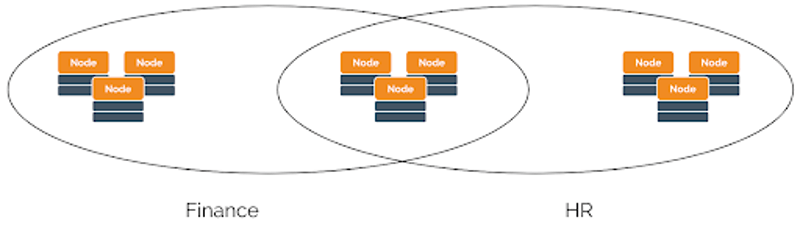
In most large enterprises it is imperative to have Identity and Access Management, especially one that provides a combination of resource and role based access management. An IAM solution is an effective way to improve security and access by limiting who has access and how much access they have to appropriate systems. The best way to deliver these increased Identity and Access Management practices is to set up a role-based access control (RBAC) strategy based upon how environments are set up. A clear distinction of access by roles or responsibilities is presented in the following example that distinguishes between Finance versus HR.
Today, Chef announces the generally available (GA) of a comprehensive Chef Automate Identity and Access Management capability which includes an enterprise-grade Role-Based Access Control framework to enable customers to more easily manage large scale implementations across teams and Project-scoped Access Control capabilities allowing administrators to delegate system management responsibilities more easily. Chef Automate’s Identity and Access Management will be available for download on April 13, 2020.
Role-Based Access Control (RBAC)
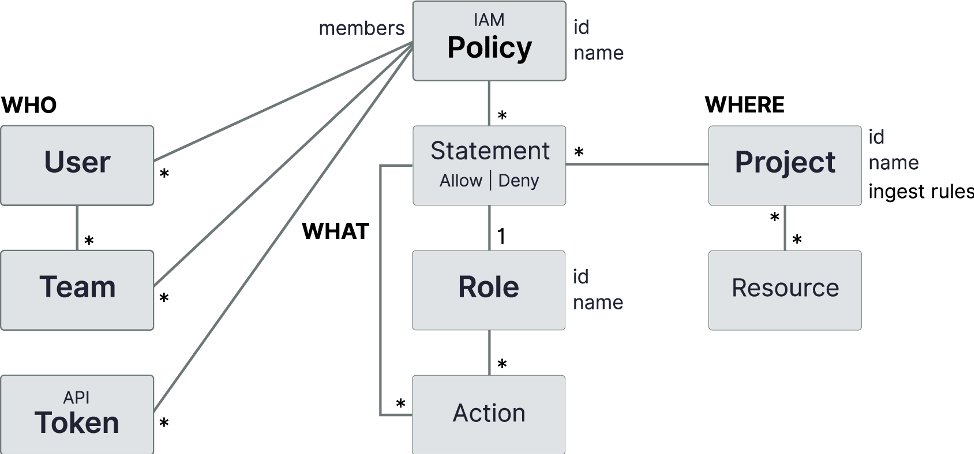
Chef Automate’s Identity and Access Management (IAM) builds on existing LDAP and SAML integrations by introducing enhanced multi-statement policies and role-based access control with a set of built-in roles to simplify typical security configurations.
Several built-in IAM roles, or a named list of actions that can be performed in Chef Automate, are provided including: owner, editor, viewer, and ingest. For more detailed information on what type of permissions each role has see the IAM Overview documentation.
Role | Description |
Owner | Do everything in the system including IAM |
Editor | Do everything in the system except IAM |
Viewer | View everything in the system except IAM |
Ingest | Ingest data into the system |
These IAM roles can be used in a policy statement to allow or deny access to the actions contained in an IAM role. You are now able to manage IAM policy membership through the user interface in addition to the REST API, giving you control over who has access to what actions. As before, IAM policy members can include LDAP/SAML users and groups plus local users, teams, and API tokens.
Custom IAM roles are also supported via the REST API and can include over 130 individual IAM actions that we upgraded to support fine-grained access control and delegation of specific responsibilities.
Project-scoped Access Control
Chef Automate’s Identity and Access Management (IAM) now also offers IAM Projects, which work in conjunction with IAM roles providing complete role and project-scoped access control in Chef Automate. This introduces a new project admin role that allows for global administrators to delegate management responsibilities more easily.
Chef Automate’s IAM supports up to 300 projects that are used in IAM policies to reduce the scope of permissions to the resources defined in an IAM project. In this example illustrated below, if there are independent business units, such as Finance or HR, Finance users will only see and have access to data related to Finance and HR users will only have access to data related to HR.
How to get Chef Automate’s IAM
Chef customers wishing to get Chef Automate Identity and Access Management will need to make sure to be on the latest version of Chef Automate v2.
To get the GA version of IAM:
New Customers (Installing Automate for the first time)
Once the latest version of Automate is installed you will have the latest version of IAM.
Existing Customers
For current Chef Automate Users, once the latest version of Automate is installed users will have access to the latest version of IAM. If you have auto-upgrade set up, be aware that the following will apply to you on the day of the release, April 13, 2020. If a customer has already been using IAM prior to this release, please see additional information:
- There will be no way to reset to IAM v1
- All IAM v1 policies will be migrated to IAM v2 as legacy policies
- It is advised that you move members of these legacy policies to the new policies and then delete the legacy policies
- If you do not want to migrate IAM v1 policies, you will need to upgrade before this release using
chef-automate iam upgrade-to-v2 --skip-policy-migration
- Anyone who had already upgraded to IAMv2 and created custom policies using infra:* may want to adjust those policies to use infra:nodeManagers:* and infra:nodes:* because infraServers is now under
infraand its intended that only admins be able to see and interact with infra servers - We recommend taking a new backup after new installation of Automate
Learn more
If you have auto-upgrade set up, be aware of what will happen once upgraded, see “How to get Chef’s Automate IAM” info for existing customers. For more information about this Chef Automate IAM release, please be sure to check out the User’s Guide.
Your feedback is always welcome so in order to continue to improve our IAM offering we hope you provide feedback by entering your suggestions in Chef’s Idea Portal.

