Following on from the recent announcement that Chef has achieved CIS certification across AWS, Azure and GCP let’s take a deeper look at how to get started with Chef InSpec on these cloud providers. Starting with InSpec v3.7.7 there is profile generation support for AWS, Azure, and GCP. This makes it easier than ever to start your infrastructure testing and continuous compliance journey with InSpec for these cloud providers.
Chef InSpec profiles provide an excellent way to organize and reuse custom controls, for more details see the InSpec Profile Documentation. GCP, Azure and more recently AWS are now supported as Open Source, standalone InSpec resource packs:
- InSpec AWS – https://github.com/inspec/inspec-aws
- InSpec Azure https://github.com/inspec/inspec-azure
- InSpec GCP – https://github.com/inspec/inspec-gcp
Each resource pack has instructions on how to set up the necessary provider credentials. For now, let’s assume that these are available and InSpec is also installed locally.
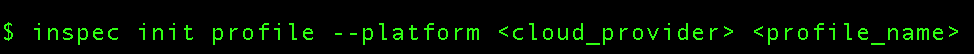
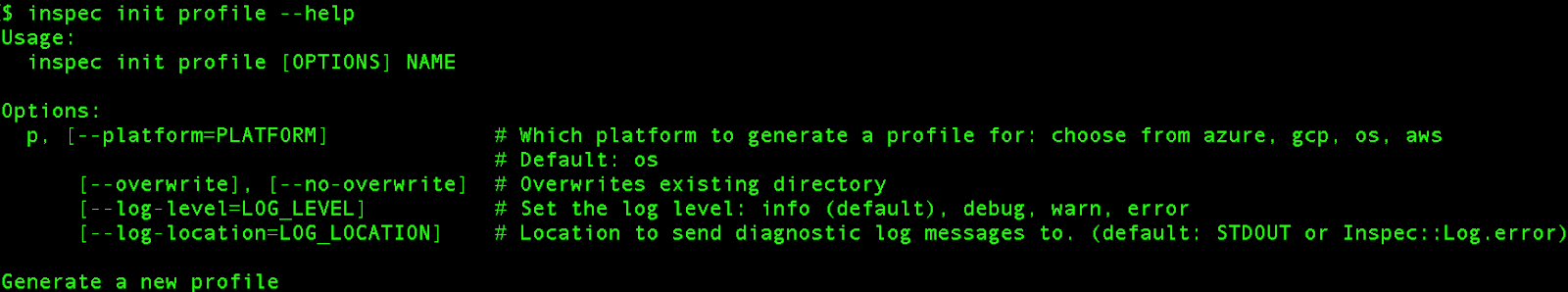
For each cloud provider, the sequence of steps is the same e.g.
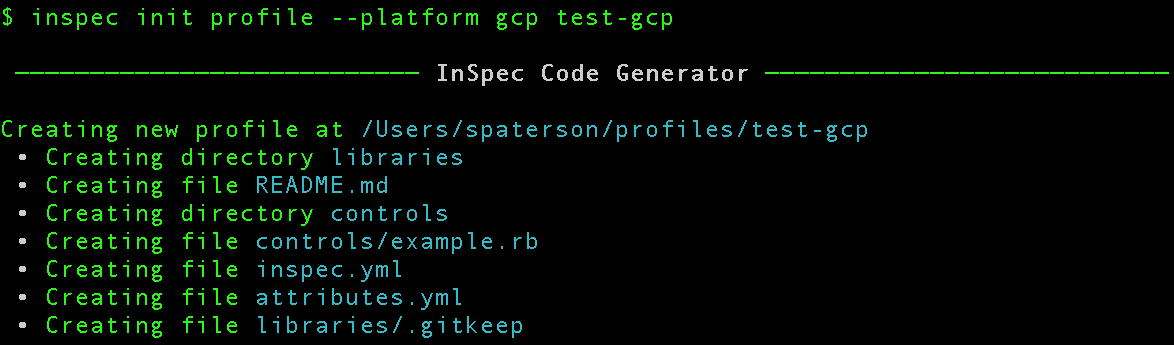
This creates an InSpec profile locally with the following structure:

As we will explore below, sample controls are supplied for each cloud provider. Sample profiles can also be generated for `os` platform resources:
Now, let’s actually run through these steps for each cloud provider.
Chef InSpec on GCP
To get started with InSpec on GCP, let’s create the profile:
The sample control this automatically generates is:
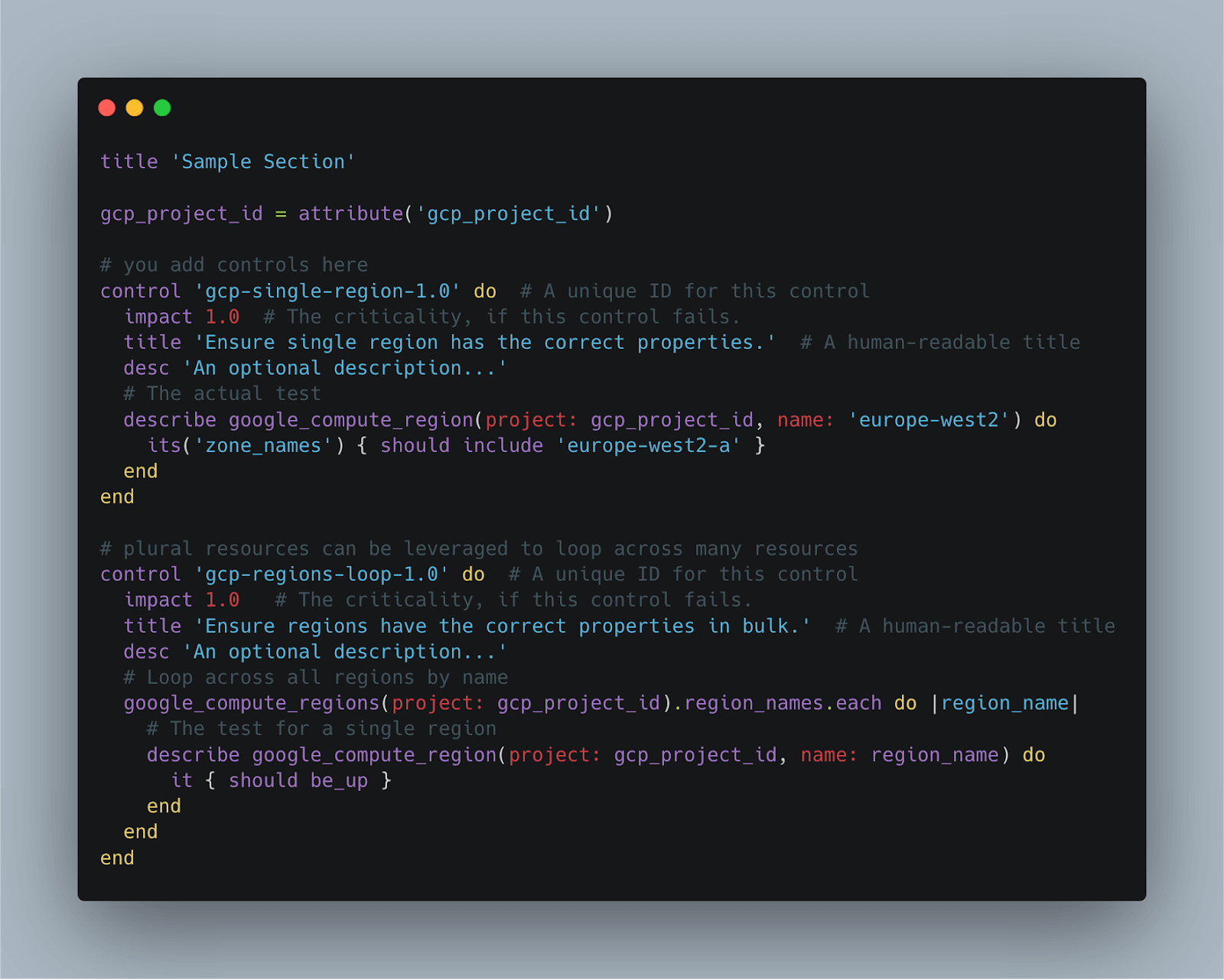
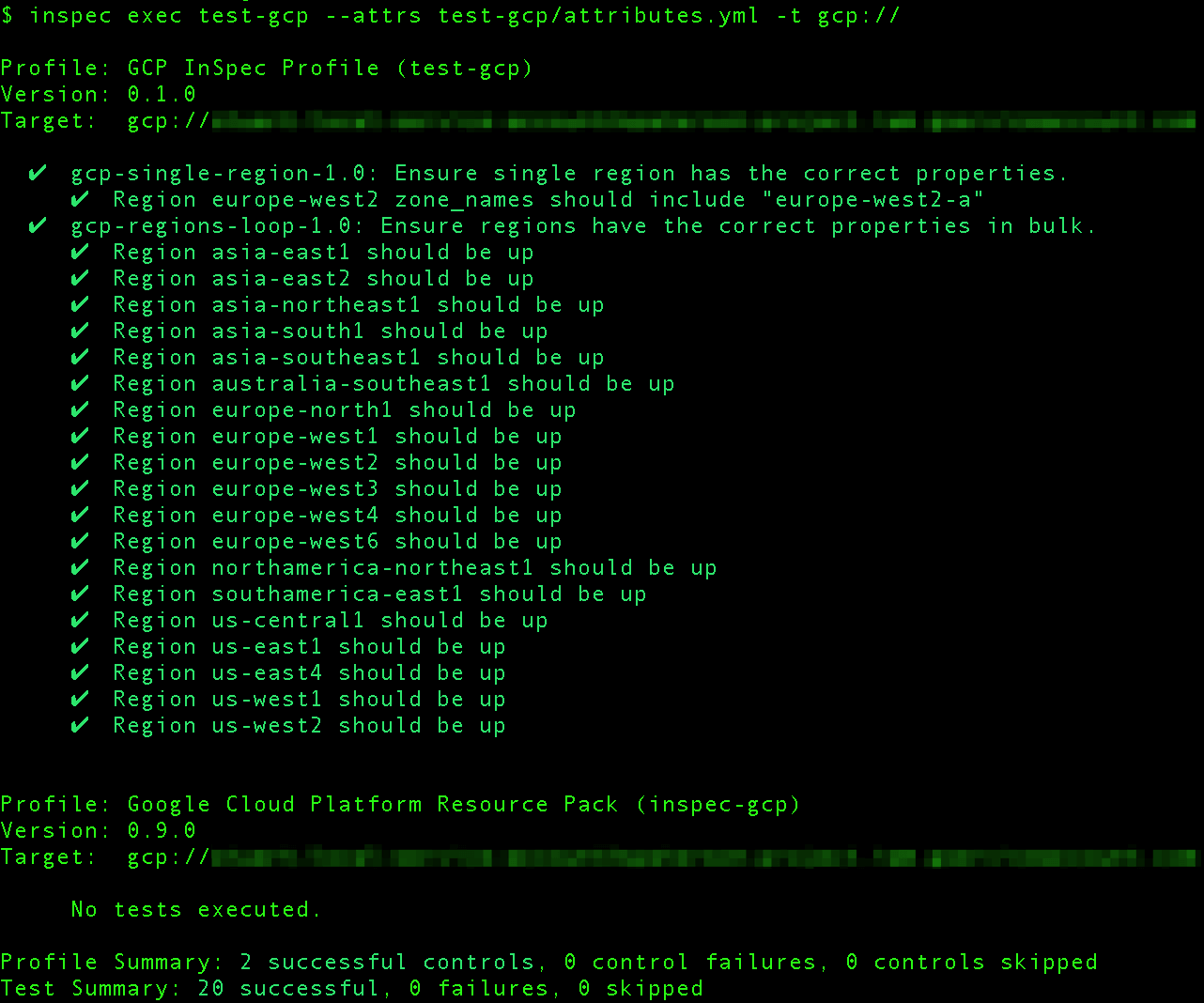
Amongst other things, this highlights how single and plural InSpec resources can be used in concert to perform meaningful checks across all GCP regions. Executing the generated profile with InSpec:
Chef InSpec on Azure
Creating the InSpec profile for Azure using the same command:

The generated example control is:
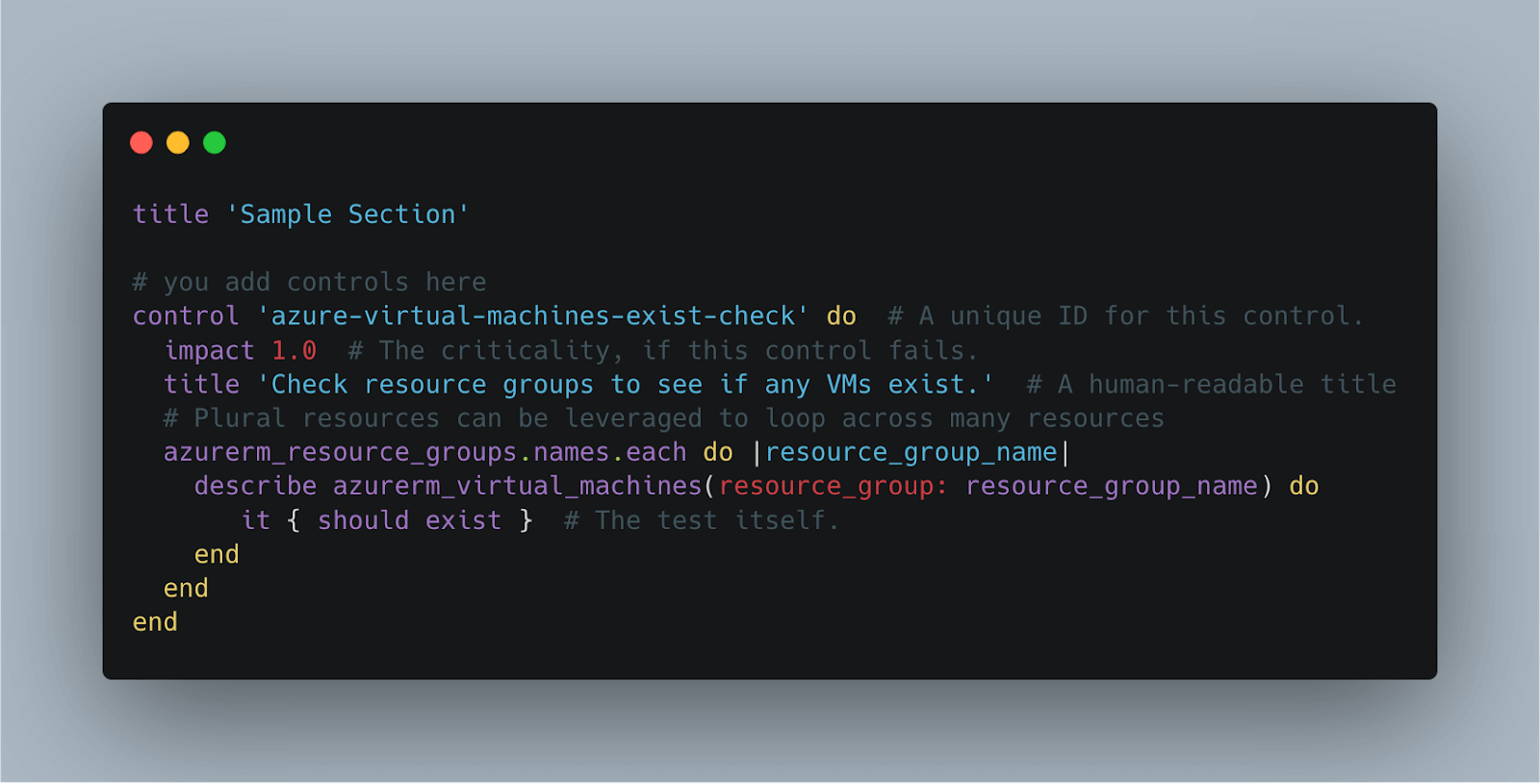
This sample control loops across all resource groups in the Azure subscription and enforces that Virtual Machines should exist in each one. Running this profile with a variety of resource groups we see:
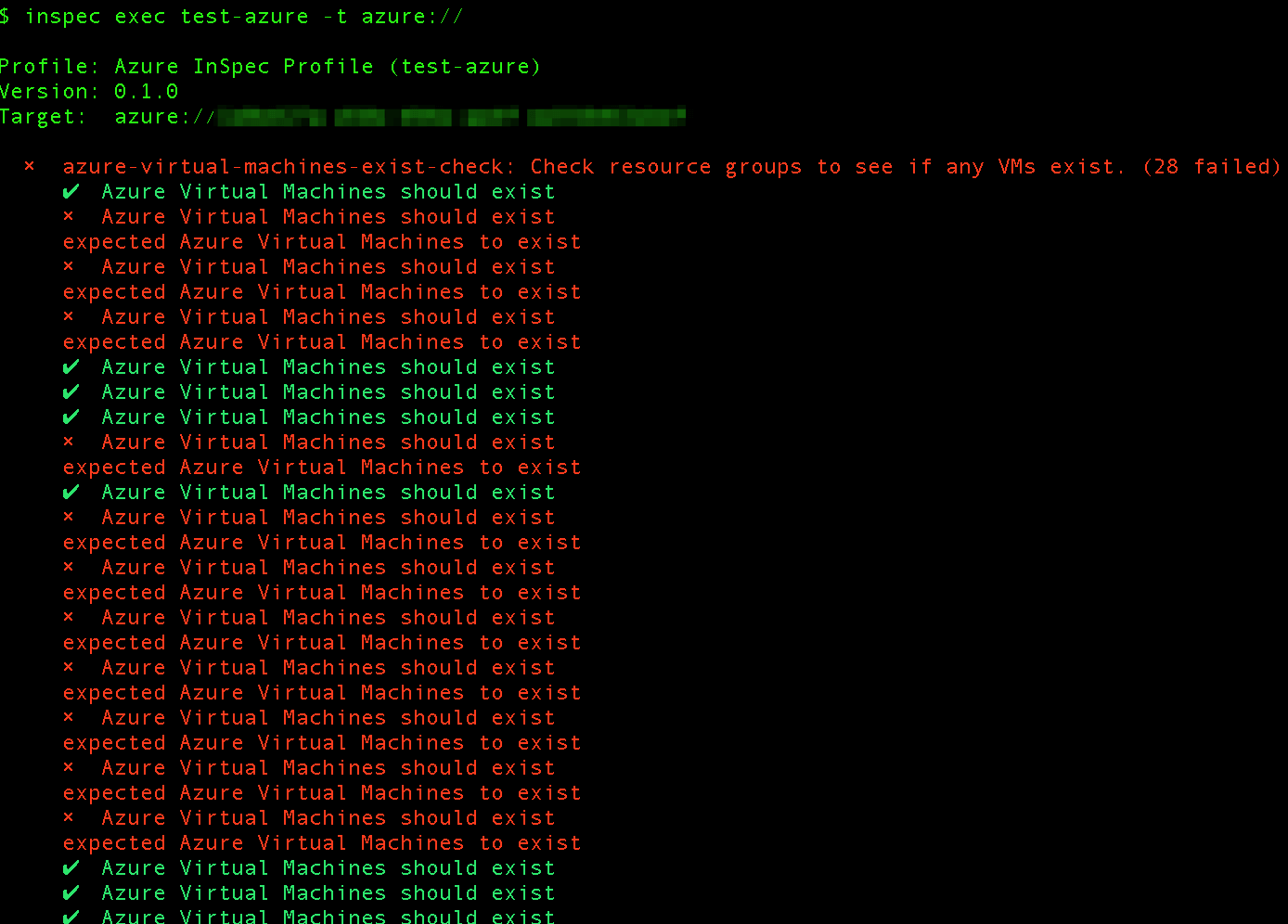
The example control fails in this case because some of the resource groups in this subscription are empty.
Chef InSpec on AWS
As part of the upcoming InSpec v4 release, the existing AWS resources previously shipped as part of InSpec have been revisited and reorganised into a standalone resource pack. The new resource pack depends on AWS SDK version 3. This can be used today following the instructions on the resource pack page. Following the same pattern, let’s create the InSpec AWS profile:

The sample control this generates is:

Here we have several examples that show: the use of attributes; conditional test execution using `only_if` and single/plural resources. Running the profile with a supplied VPC identifier (via the `attributes.yml`):

This is a nice opportunity to highlight the multi-region capability of InSpec AWS resource pack. The default region in this case is `eu-west-2` but our sample control allows to target resources across all regions with a few lines of readable test code.

Summary
In this post, we explored how easy it is to get started with InSpec profiles across AWS, Azure, and GCP. The sample controls for each provider showcase core InSpec functionality and are a good starting point for creating tailored controls according to your infrastructure testing or continuous compliance needs. Resource documentation organised by cloud providers is available here. InSpec cloud resource packs are Open Source and welcome suggestions for improvement or contributions from the community.

