The Chef InSpec Best Practices Series is designed to help Chef users leverage the power of Chef InSpec to test, validate and audit system configurations across their environment. In this first blog and webinar, “Scaling Infrastructure Testing with Chef InSpec”, we look at how InSpec can be used to test Chef Infra configurations and validate security and compliance policies across your entire IT estate.
Keeping infrastructure secure is among the most fundamental aspects of IT operations management. However, when IT assets grow in number and become more diverse in terms of operating system and hosted environments, managing security and meeting compliance requirements becomes challenging, especially when controlled manually. Chef InSpec eliminates the need to rely on manual processes that not only consume enormous amounts of time but also are incredibly unreliable.
By integrating security earlier in the development cycle (also known as ‘Shift Left’ testing), developers are more likely to find errors before reaching production, saving time, effort, and enabling secure versions of changes to be delivered. This leads to improved overall security and compliance postures of infrastructure within the organization.
What is Chef InSpec?
Chef InSpec is a security testing solution that defines policies as code and provides continuous visibility into compliance status across all systems and teams. InSpec is platform agnostic and supports multiple operating systems (Windows, Linux, Mac, AIX) and platforms (physical servers, containers, cloud APIs) ensuring audits are continuous, consistent, and quick across heterogeneous IT estates. With InSpec, organizations can:
- Test the state of everything – from files, packages, users on a server to security groups on cloud resources
- Detect violations by comparing the actual state of systems with the desired state as defined in the policy
- Understand security and compliance status of systems through detailed reports and plan remediation measures
- Scale policies across distributed systems and continuously test systems
- Streamline testing throughout the software delivery process
Easy-to-read controls describes system state expectations in ways that can be mapped directly to policies defined by Chef Infra, providing tools and insights into how to remediate any misconfigurations uncovered in audits. Integrating Chef cookbooks with Chef InSpec profiles has been simplified, so if you are already creating cookbooks using Chef Workstation and Test Kitchen, you have everything you need to become a Chef InSpec user.
Testing Chef Infra Configurations with Chef InSpec
InSpec allows users to compare the actual state of their systems with the desired state that is described through easy-to-read and easy-to-write code. Cookbooks that include infrastructure tests such as configuration updates, application installations, etc. can be used in the Test Kitchen to test in local or CI environments and changes can be validated before being applied across large heterogeneous IT fleet.
Validating Security and Compliance Policies Across Your Entire IT estate
InSpec also allows security and compliance policies to be defined as standardized code making it simpler to ensure endpoints within organizations are always secure and conform to regulatory and industry standards. Cookbooks with security tests defining firewall rules, ports, SSL, and other baselines, and compliance tests defining regulatory or industry requirements can be tested in Test Kitchen and validated. Chef offers over 500 CIS and STIG based profiles prebuilt with hundreds of controls to test such vulnerabilities.
Getting Started with Chef InSpec
Getting started with InSpec is easy. Users can download Chef Workstation which comes pre-configured with all Chef tools including InSpec, Infra, Habitat, Cookstyle, Test Kitchen, Knife, and Automate. Workstation comes with 100s of built-in resources and content templates that make it easier to get started with security and compliance profiles. Once you’ve installed Workstation, working with InSpec is made simple. Ideally, there are just three simple steps to get started:

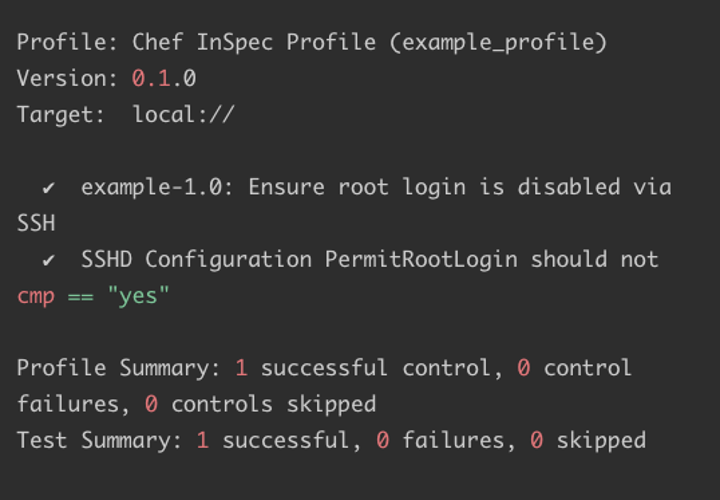
- Write the test:
Create simple Ruby-based tests to verify your expected state against the current state of your systems - Run the test:
Execute your test against your target system locally or remotely with one simple command - View test results:
See which tests failed, passed and skipped the expected state against the current state of your target system, in one simple output
For more information watch the “Scaling Infrastructure Testing with Chef InSpec” webinar where we walk you through the functionalities of Chef InSpec and show how you can use InSpec to test infrastructure configurations across operating systems and environments and ensure healthy security and compliance postures across the entire IT fleet.