IT administrators requirements in 2019 appeared to be very different from those since the beginning of 2020. In 2019, for example, device management was predicated on an IT department's ability to quickly gain physical access to most devices within their IT ecosystem. Most organizations did not need a fully remote help desk environment for troubleshooting techniques.
Since then, many of our previous plans have changed for the foreseeable future as we look ahead to IT trends for 2022 and beyond. Even after the COVID-19 pandemic has passed, many organizations will continue to be fully remote or, at the very least, encourage remote work, necessitating a variety of tools for IT to achieve their department's objectives.
According to Evans Data Corporation, professional developers will increase by more than 28 million by 2024.
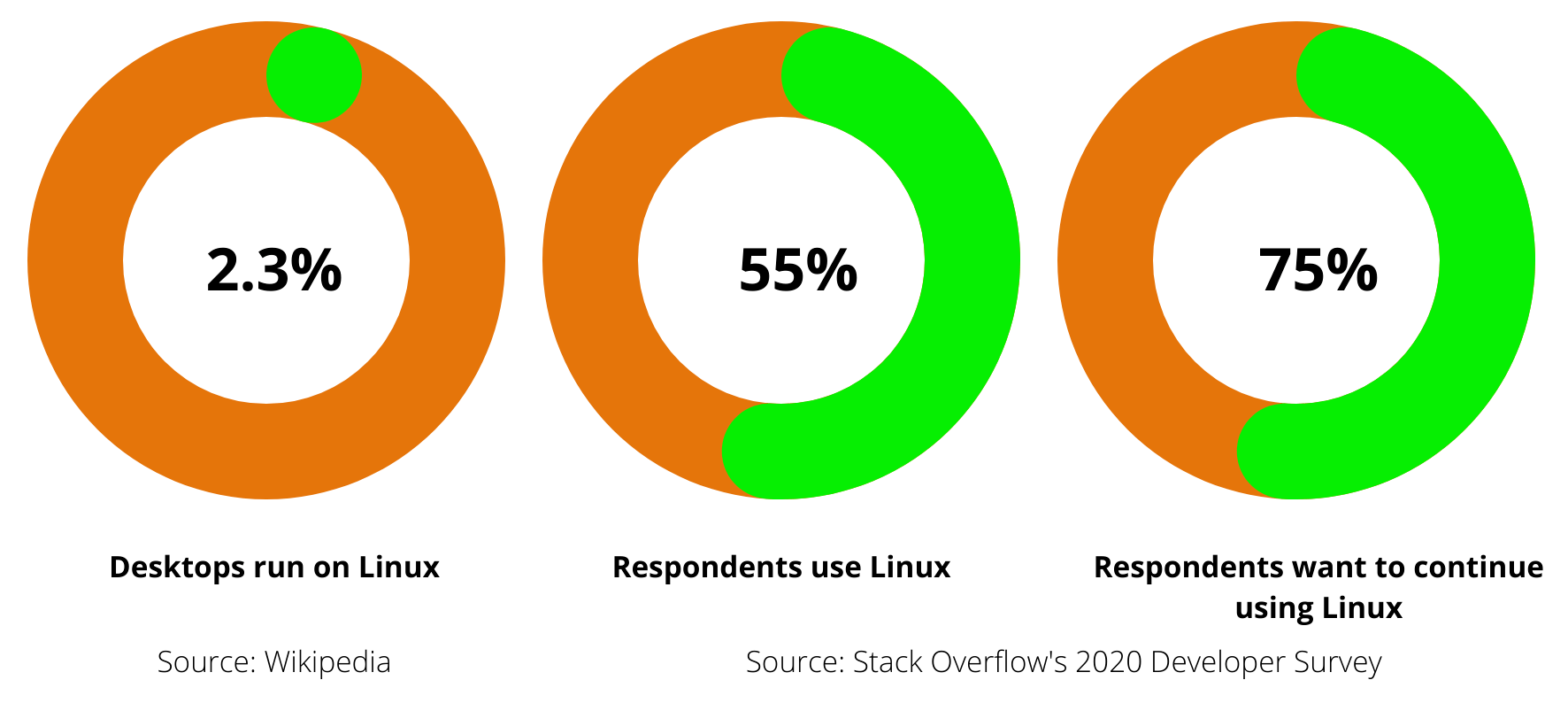
Long-term integration of Linux systems and infrastructure into IT operations is expected in organizations that use Linux. To automate Linux systems, IT administrators must have complete control over their security and configuration settings and the ability to monitor systems afterward to ensure everything is running smoothly. Unfortunately, Linux infrastructure is not generally straightforward to automate, and without extra tooling, some administrators may face a long road to achieving their automation targets.
But, before we get into what it takes to manage your Linux laptop/desktop fleet, let's look at why organizations lack control and visibility over their Linux endpoint devices in the first place.
Unregistered Devices
Many endpoints currently connected to corporate networks are not official corporate assets. Because IT departments don't own these devices, they can't quickly assess or monitor them to ensure they get the updates and patches they need. This not only makes them vulnerable to threats, but it also makes them a relatively unknown threat vector, posing a threat to the entire fleet of devices.
Mobility of Devices
Another significant barrier to visibility is mobility. Endpoint devices were once considered corporate assets kept behind the corporate firewall. Users of these endpoint devices today can connect to corporate resources, access corporate data, and even work on it using a variety of applications. They don't need to be connected to a VPN to access physical or cloud-based resources, becoming more common. The fact that these devices spend the majority of their time related to non-corporate network resources significantly reduces IT visibility, according to a 2017 Ponemon Institute report titled "The Cost of Insecure Endpoints." Two-thirds of IT professionals admit to having no visibility into endpoints that connect to the network regularly when they work outside of it.
Shadow IT
Employees can easily install and run traditional and cloud-based applications on their phones and computers, as well as on corporate-owned assets assigned to them, without having to go through IT. If IT administrators don't have insight into all of the programmes operating on these devices, they won't be able to verify that essential access controls are in place to mitigate threats or govern the spread of data and other business assets.
Security Solutions for Isolated Endpoints
Endpoint security has traditionally been treated separately from the broader network security plan, and it has frequently been the responsibility of the IT admins team rather than the security team. However, as endpoints become a more critical part of the extended network ecosystem, this approach not only limits visibility and control but also makes it difficult to assess a device's security level and take the necessary automated steps in the event of a compromise due to a lack of access to vital threat intelligence.
How does Chef Desktop help you gain control & visibility into your Linux Laptop?
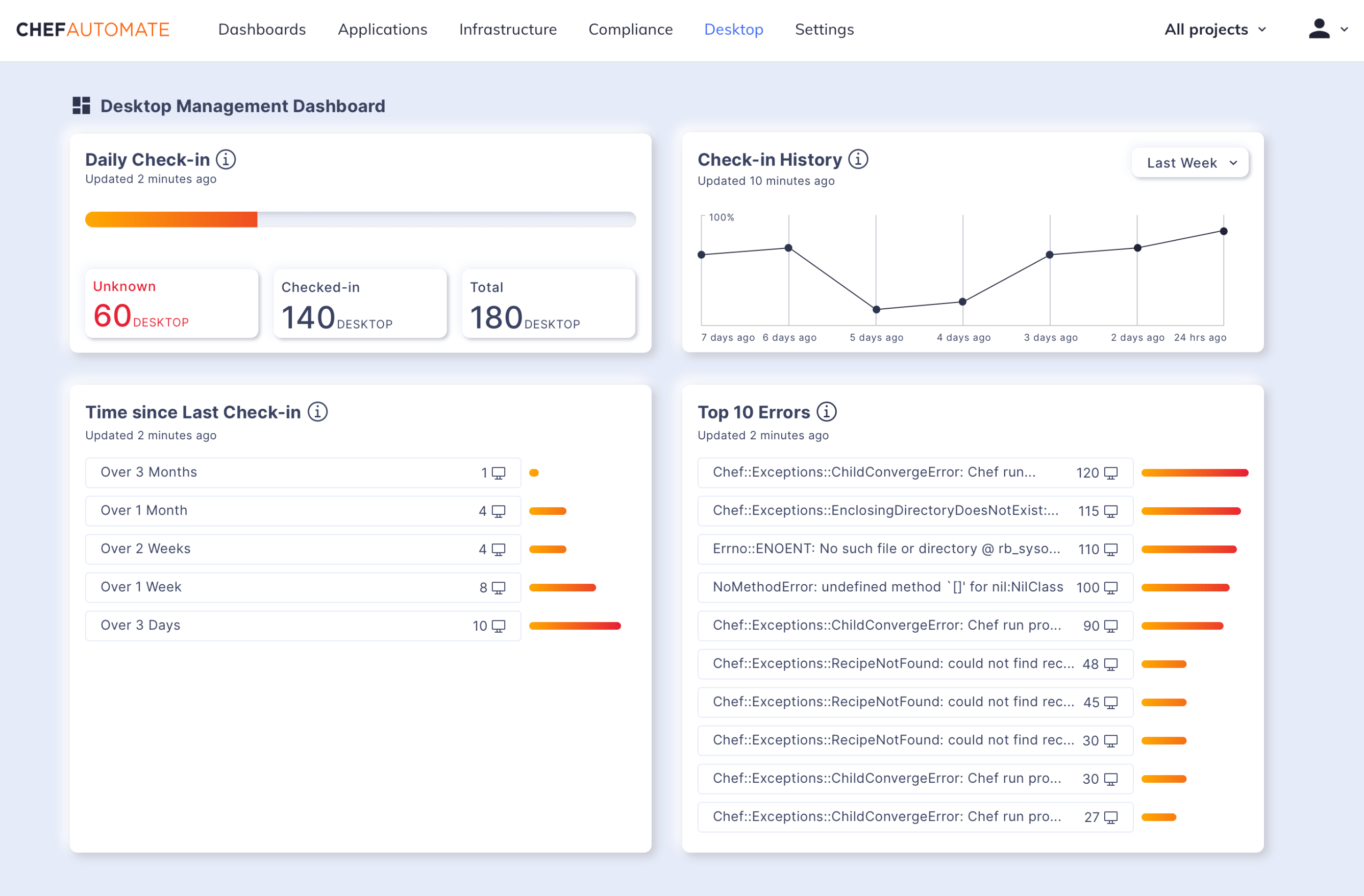
Managing your Linux devices in real-time
Having complete visibility over your IT asset inventory for security and productivity monitoring is critical. Chef Desktop scans your endpoints in real-time, detecting all available software and hardware in your network. Important metrics to keep an eye on including the number of unknown, checked-in, and total devices in your fleet, as well as devices installed and outdated and rarely used apps. As an outcome, it keeps a constantly updated and monitored inventory of IT assets.
Maintaining endpoint health with solid security controls
Every day, numerous activities take place at an endpoint. To detect suspicious activity, it is critical to keep an eye on everything. Chef Desktop keeps track of and monitors all your Linux endpoints, performing rigorous and regular security checks. It also conducts regular endpoint health checks to protect your endpoints, enforces firewall policies, quarantines, or isolates unnecessary devices, kills rogue processes and services, hardens system configurations, and performs remote system tune-ups and disc clean-ups.
Identifying and eliminating unauthorized devices and applications
Allowing any random device or application in the network will gouge a hole in IT security and employee productivity. Disabling or blocking illegal devices and programs from entering your network is critical. Chef Desktop implements a robust application and device control policy to safeguard your fleet of machines from malicious activities irrespective of their OSs (Operating System).
Enabling remote access
Continuous monitoring of your endpoints requires security tasks to be executed even remotely, without relying on physical access of devices. Chef Desktop helps achieve this without worrying about connectivity and maintenance issues.
Chef Desktop allows IT managers to:
- Reduce costs by eliminating time-consuming manual processes.
- Configure your entire Linux fleet in a consistent, policy-driven manner.
- Maintain visibility into the overall status of the fleet.
- A robust dashboard provides detailed visibility across their Desktop fleet.
- Use automation and time-saving processes to boost efficiency and productivity.
If any part of this blog has piqued your interest, scroll down, and register for our upcoming webinar right away. Chef's easy-to-implement configuration management capabilities can assist IT teams in managing and overcoming some of the challenges they face when managing large Linux laptop fleets.
Join Our Webinar to Learn More
Join the discussion with Chaithra Mailankody, Associate Product Manager, & Sudeep Charles, Senior Product Marketing Manager at Progress Chef Desktop, to learn how to:
- Manage Linux laptops and desktops for any fleet size automatically.
- Use a single tool to manage Linux and other platform-oriented endpoint devices (Windows, macOS).
- Enforce enterprise security and compliance standards across your entire Linux fleet continuously.