A report created by Gartner predicted that the worldwide container management revenue will grow from a small base of $465.8 million in 2020 to a robust $944 million in 2024. With more than 75% of organizations
adopting Kubernetes
in 2023, it is hardly a matter of surprise that Kubernetes is a popular and most widely used container orchestration system in IT stacks around the globe while its worldwide popularity continues to grow.
Despite its ubiquity, finding Kubernetes security specialists remains a difficult task. Moreover, with industries rapidly taking to the cloud and the subsequent growth of cloud-native deployments, the demand for Kubernetes security professionals' services is vastly outpacing the supply. Therefore, it would be vital to simplify securing K8s implementations and lower the skill barriers.
What is Kubernetes Security Posture Management (KSPM)?
Kubernetes Security Posture Management uses automation to locate and fix security, configuration, and compliance issues affecting all Kubernetes components. It is a comprehensive set of tools that may issues that are likely to go unnoticed during manual audits.
Although different tools may handle KSPM differently, KSPM workflows have a few fundamental components.
# 1 Set Security Policies
KSPM tools are typically driven by policies that specify compliance and security risks. Most KSPM platforms have pre-built policies, but administrators can create their own. For instance, to uphold the principle of least privilege and remove any access privileges for inactive users, you can build Role-Based Access Control or RBAC policies. As a result, any RBAC misconfigurations linked to unauthorized entry requests from potential hackers will be discovered by KSPM.
# 2 Configuration Scan
The KSPM tools can automatically scan a Kubernetes environment using security and compliance benchmarks. Then, for each resource they assess, they look for configurations that differ from the benchmarks defined by the security and compliance team or standard regulatory benchmarks like CIS, PCI DSS, SOC2, HIPAA etc. For instance, RBAC policy violations such as compromised service accounts that do not follow the least privileged access principle or inactive accounts from previous employees who have left the firm can be checked for using KPSM.
# 3 Detect, Evaluate, and Alert
When a policy violation is found by the KSPM tool, it can typically assess its severity and, if required, publish an alert or notification. In addition, it can provide remediation guidance to help remediate the policy violation.
Key aspects of KSPM
Compliance Enforcement
Organizations that must adhere to strict compliance regulations find KSPM highly effective since it uses policy engines to assess configurations and pinpoint hazards.
For instance, businesses can automate compliance management within their Kubernetes clusters by establishing policies that guarantee that any data managed or accessed by Kubernetes is stored in ways compatible with frameworks like
CIS or SOC2.
Third-Party Configurations Validation
Teams commonly import or borrow resources from the upstream in the Kubernetes ecosystem. For instance, you may utilize a deployment file you found on GitHub or download container images from a public Docker Hub registry. The third-party publishers of such resources may or may not follow the same security procedures as your team.
KSPM offers a method for vetting external resources for potential security issues. As a result, you can manage the security risks involved while accessing the vast resources the Kubernetes community offers.
Keeping Security Active while Clusters Evolve
A secure configuration for one version of Kubernetes may no longer be secure if you switch to a new version because Kubernetes is still a dynamic technology.
For instance, Kubernetes declared the deprecation of pod security policies in 2021, which were formerly a vital tool for implementing access controls across pods. The Kubernetes versions that are currently in use continue to enforce pod security limitations.
However, this support will end with version 1.25.
Let's say you still utilize pod security policies when you move to version 1.25. In that case, a KSPM tool might warn you that Kubernetes is violating your policies and that you should switch to something else, such as Kubernetes security contexts or
custom admissions controllers.
Human errors and oversights
is a method for verifying the security of the configurations you use to control Kubernetes resources. No matter how diligently engineers strive to develop secure configurations by default, there is always a chance that human error or oversight will result in less secure setups. Teams can find and fix these issues with KSPM before they lead to breaches.
KSPM and Cloud Security Posture Management (CSPM)
, a class of IT security technologies created to find and address misconfigurations and compliance concerns in the cloud, is already a very well-known and popular concept for industry professionals working in the cloud. In addition, the automation features available on make the task of safeguarding cloud service stacks easier. More than ever, operators are using Kubernetes to deploy workloads, and Kubernetes Security Posture Management (KSPM) has established itself as a crucial ally to CSPM.
The difference between the two lies in that KSPM focuses on the unique problems associated with Kubernetes implementations and not on the cloud. KSPM tools were created to evaluate and safeguard specific resources and structures, such as Role-based Access
Control setups in Kubernetes, which have unique considerations. Also, organizations that use Kubernetes to manage their workloads require automated security technologies specifically designed for those use cases.
Using Chef for KSPM
Chef Container Security solution provides KSPM capabilities to protect Kubernetes elements like Pods, Network Policies, container network interface (CNI) and Secrets.
The engine behind Chef Container Security is Chef InSpec, a framework for testing and auditing your applications and infrastructure. Chef InSpec works by comparing the actual state of your system with the desired state that you express in easy-to-read
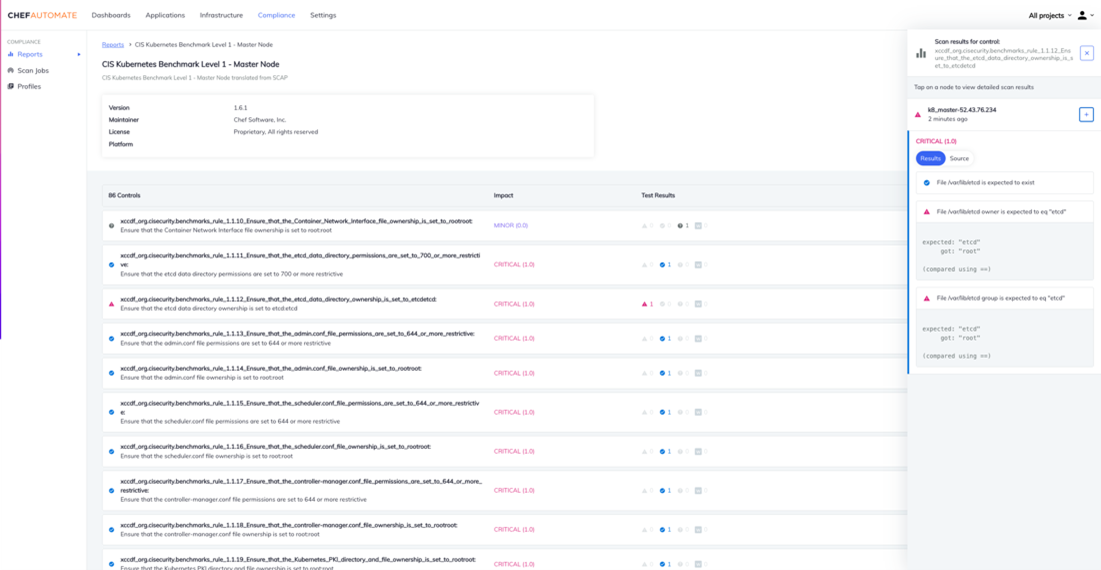
and easy-to-write Chef InSpec code. With the policy-as-code approach, it is easy for users to create or customize policy definitions or even use standard benchmarks provided by Chef like the CIS Kubernetes benchmark.
Hence, the same workflow and processes can be used to assess the security posture of any container environment. Chef maintains and keeps adding to an exhaustive library of premium content of profiles and resources. Apart from KSPM, Chef also provides resources and profiles to secure your Docker, OpenShift and Podman environments.
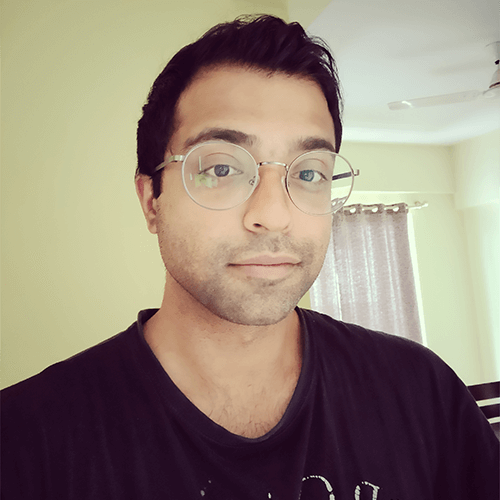
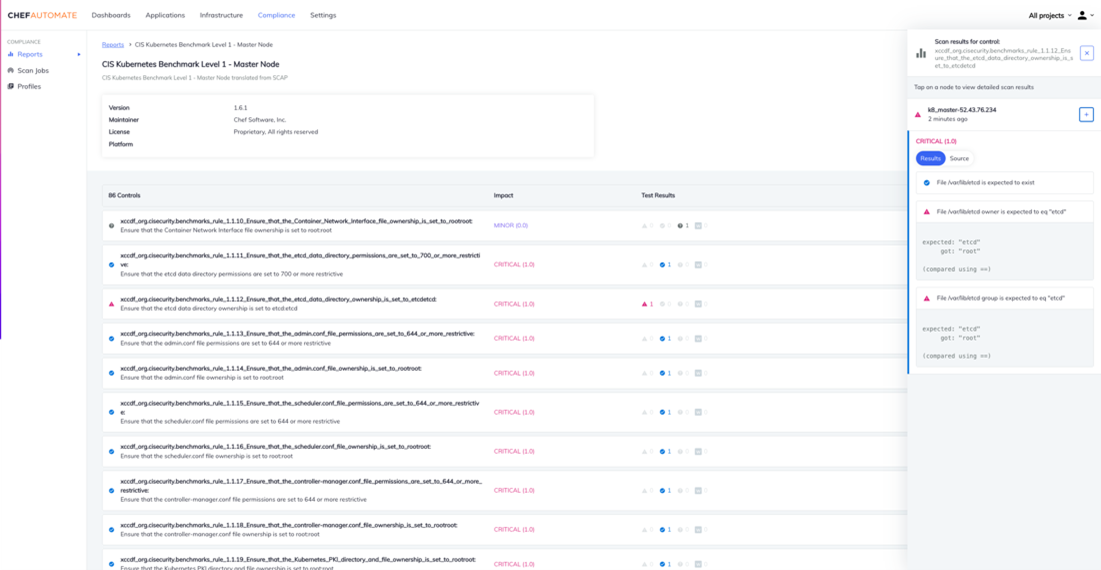
Using the CIS Kubernetes Benchmark, the security posture of your Kubernetes clusters can be continuously assessed. In the following use case, we showcase how Chef Automate can be leveraged for container security; to check the security posture of the
Kubernetes master node. It is accomplished in four simple steps.
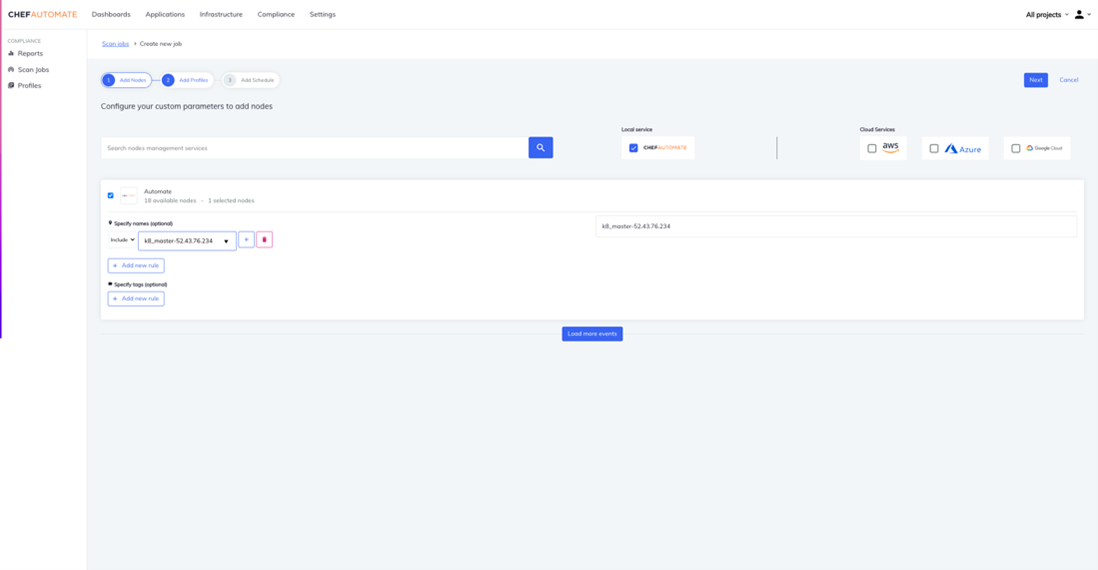
Step 1 - Integrate your Kubernetes Host
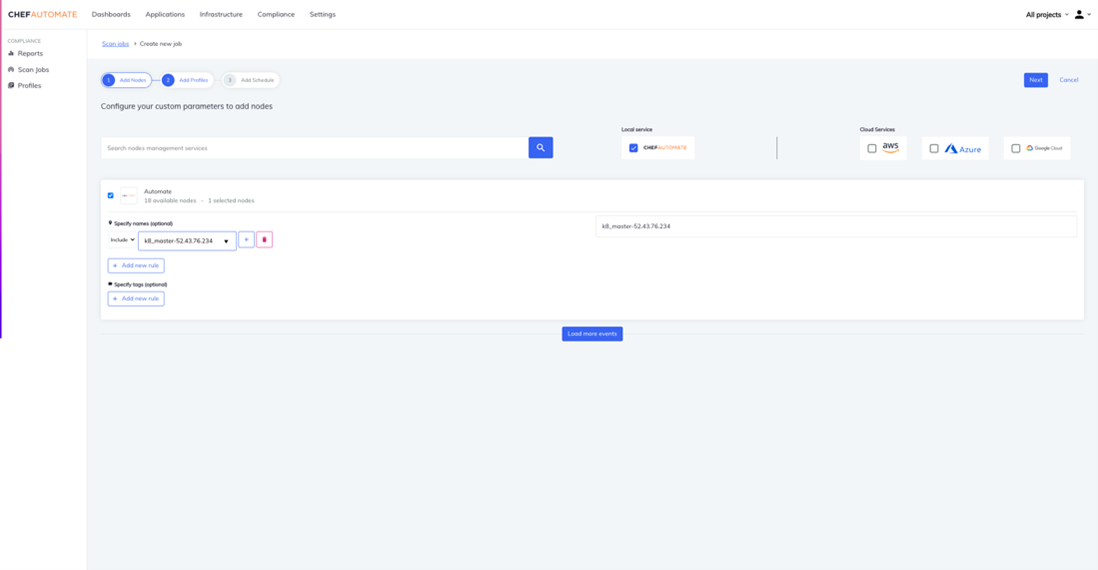
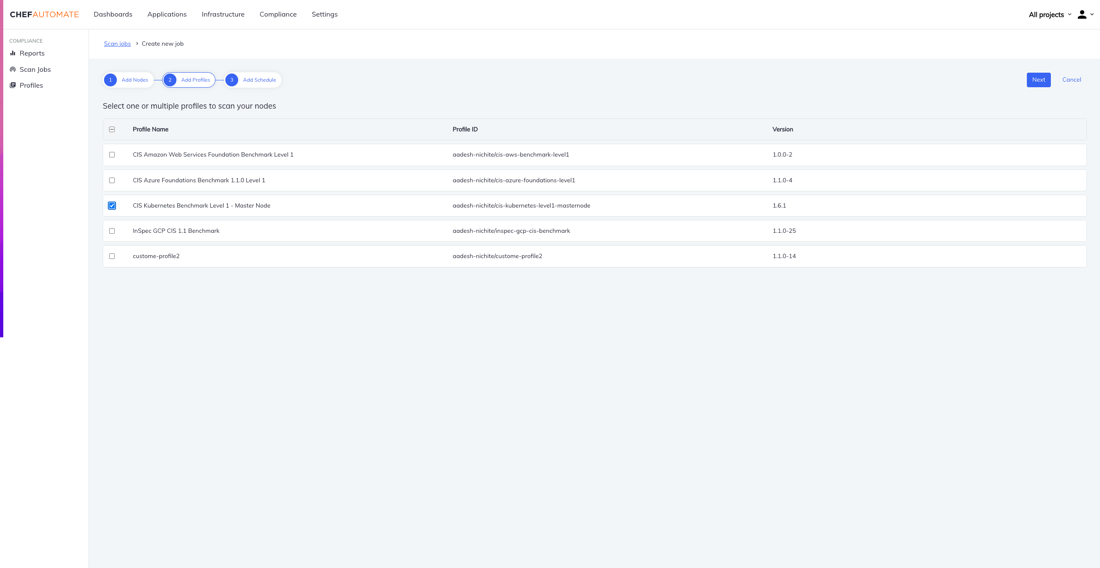
Step 2 - Select the CIS Kubernetes Master Node profile
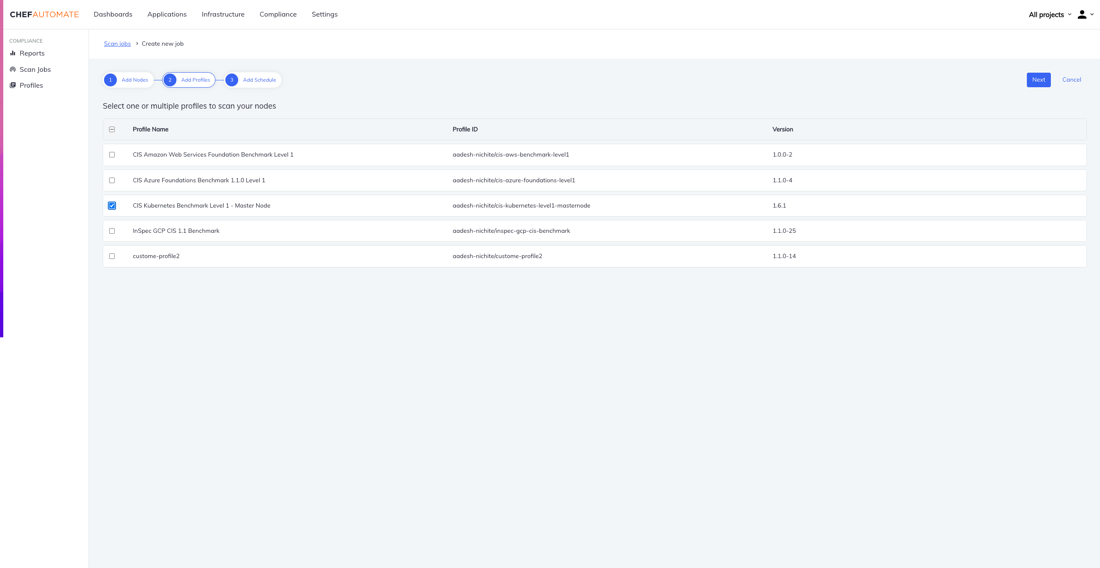
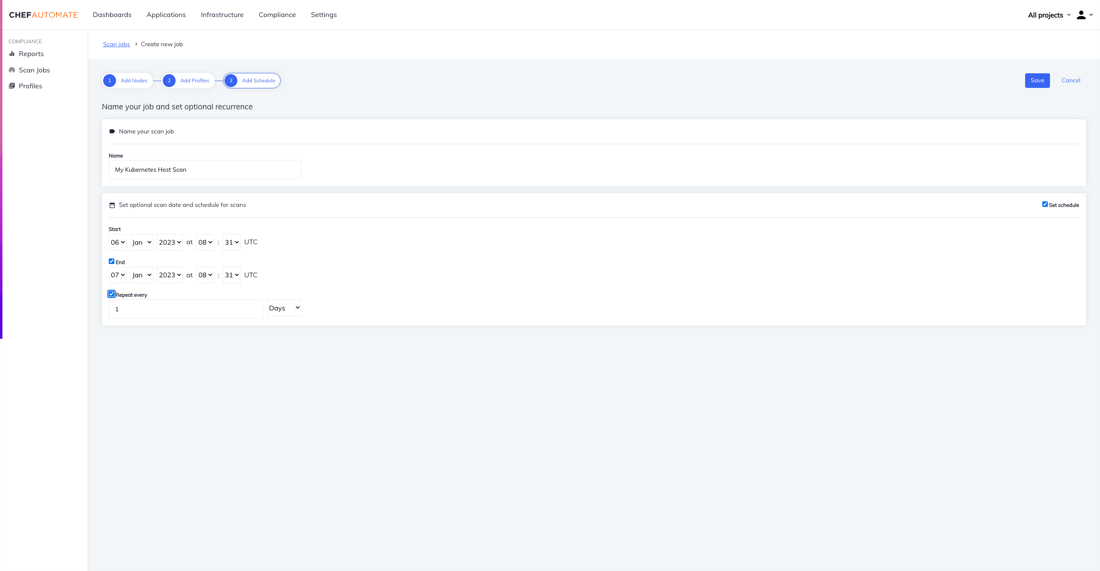
Step 3 - Schedule regular scanning of the Kubernetes Master Node
Step 4 - Access the report to view the security posture of your Kubernetes Master Node
Summary
Any organization using Kubernetes for service delivery can benefit from KSPM's integration into its container landscape. Using KSPM saves organizations precious time and money. A valuable resource that can be used for innovation, designing better and more modern products or be used for enhancing customer experiences.
Chef Cloud Security allows you to ensure your Kubernetes clusters, cloud accounts and other container environments are compliant with compliance benchmarks or your internal security policies. Find out more about how Chef Cloud Security can secure
your container and cloud environments by visiting our various resources:
To learn more about securing your Kubernetes environment, contact us today!