The cadence of compliance audit cycles can greatly impact any organization's compliance and security risk levels. Security and compliance audits should not be an annual or bi-annual process that takes months to complete. In such cases, security vulnerabilities are left unresolved for longer periods, compromising IT security and impacting the organization's compliance posture.
Most organizations find it difficult to conduct regular compliance audits as it’s a time-consuming and resource-intensive process that is manual and difficult to automate. It involves implementing security policies, ensuring compliance benchmarks are followed and validating configuration changes against existing policies. Chef InSpec simplifies the entire compliance audit process through code, making it possible to automate the process. This blog focuses on some advanced features of Chef InSpec, such as waivers, that help streamline compliance audits.
Chef InSpec for Continuous Compliance
Continuous compliance requires continuous visibility into your entire IT estate's compliance state, which is possible only with the right compliance processes and management tools. In most organizations, increasing release velocity is a priority, which usually means deprioritizing other time-consuming and resource-intensive processes such as compliance and security audits. Maintaining security and compliance strategies while simultaneously improving the pace of software delivery is key to implementing continuous compliance.
Chef enables compliance and security automation with its "policy as code" approach. This approach integrates security and compliance audits earlier in the development phase, lowering security risk and automating compliance to reduce the strain on delivery timelines and resources.
Chef InSpec is an automation testing tool for both Ops and Security designed to:
- Run frequent audits to identify and remediate misconfigurations.
- Provide compliance visibility across the organization.
- Validate current security and compliance levels.
- Ensure the entire IT estate is consistently compliant with external regulations.
In addition to compliance testing, Ops teams can use Chef InSpec for operational assurance and integration testing. With "policy as code," all the test requirements are expressed in code, allowing different teams to collaborate better. It can also integrate with existing CI/CD solutions so developers can implement testing early in the development cycle without creating bottlenecks in the process. Chef InSpec can detect compliance issues faster as every code change is tested before it is pushed to production.
Chef InSpec Waivers
Chef InSpec code is used to create tests for a compliance audit, and these tests include controls that need to be validated. During compliance audits, certain policies or controls may need to be overridden in a specific scenario, and there could also be other variables that can impact the success of the audit.
Chef InSpec offers a “skip control” feature to exclude or “skip” specific controls in an audit. But this feature has a limitation; it does not explain when or why an exemption was implemented and if it is still relevant. Chef introduced the “waivers” feature to address these concerns when using the skip control functionality.
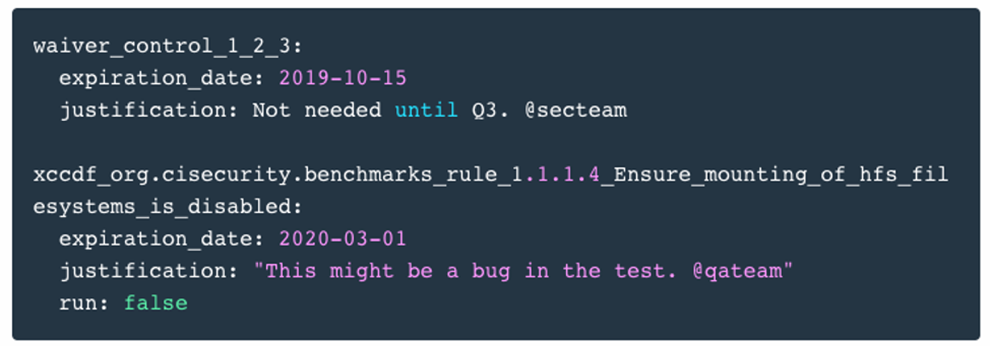
Fig 1: Chef InSpec Waiver
The waivers feature's purpose is to indicate when a control is exempted, for how long, or when the exemption expires. For example, a security fix release is scheduled for a known security deviation, but an audit runs before this release. In such a scenario, the audit will flag the same security issue, making the audit result irrelevant. In such a scenario, the audit can be configured to "waive" the control allowing the audit to pass without flagging the known vulnerability.
Waivers help maintain operational continuity as you can easily track exceptions in the compliance posture and ensure these exceptions are removed as planned. For example, in the above scenario, the waiver will expire as configured and is automatically enabled for the next audit.
A Chef InSpec Waiver uses a YAML input file that defines:
- Id of the waived control.
- Justification – a short description explaining why the control should be waived.
- Waiver start and end date – if the end date is not defined, then the control is waived permanently.
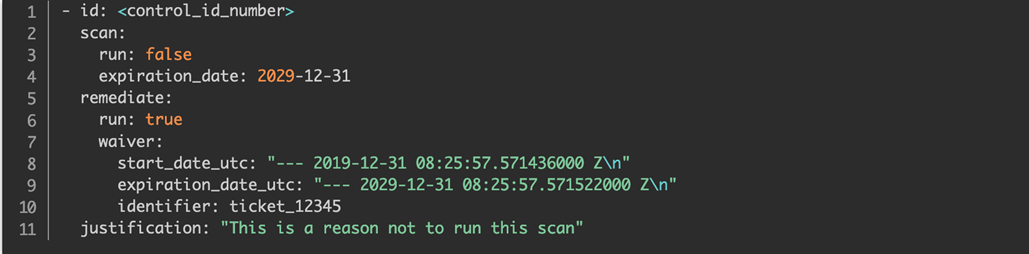
Fig 2: Chef InSpec Waiver defined using YAML
Compliance audits can be easily streamlined using waivers. Cookbook modification is not required whenever a control needs to be exempted. This means that there will be fewer failures during a scan as exceptions are marked and skipped during every scan. The end date determines whether a control is to be remediated or if the waiver is permanent. This eliminates the need to edit waiver configuration, automating the entire process of managing controls.
Once waivers are set up, it is provided as input when running an audit. The audit results, including the waiver details, can then be viewed in Chef Automate. Chef Automate gives DevOps and InfoSecOps teams a single platform to maintain compliance efficiently, and there is complete visibility into the compliance posture of the entire organization.
To summarize - waivers are an additional Chef InSpec feature that automates the skip control process.
- Waivers are set up for specific controls for a period of time.
- Audits will skip the control during the waiver period.
- When the waiver period expires, the scan is automatically enabled.
- It provides an automated and effective method of skipping controls that don't impact the organization's compliance posture.
- Waivers provide detailed information on the exempted control – why was it waived, and for how long?
- The waiver details, along with the audit results, can be viewed in Chef Automate.
Watch this video to learn more about compliance audits and implementing waivers.