If you have anything to do with IT infrastructure, operations management, or DevOps, you might have come across the term 'system hardening'. While system hardening seems like a regular everyday activity in large IT teams with diverse infrastructure, the use and benefits cover a wide range of things.
In this blog, we’ll explore what system hardening is, why it is needed, what the benefits are and finally, how Chef enables DevSecOps teams to harden heterogeneous systems with speed and ease.
What is System Hardening?
System hardening is a method of preventing cyberattacks, enabled by reducing vulnerabilities in servers, applications, firmware, and other areas. System hardening is achieved with the help of infrastructure and security management tools that help audit all systems, detect potential attack vectors, and minimize the attack surface.
Given the impact of Cybersecurity attacks on organizations, system hardening has become a strategic defense against such attacks by closing system loopholes that attackers frequently use to exploit systems and gain access to sensitive data.
Some critical activities associated with system hardening include:
- Deleting or disabling systems that are no longer in use
- Limiting permissions
- Removing superfluous applications, ports, features or user accounts
- Monitoring vulnerabilities
Ideally, running vulnerability scans is a great place to start since they reveal missing patches, security updates, and open ports that can serve as entry points for an attack. Further, system hardening also demands that default passwords of services and applications are changed, strict firewall rules are applied to restrict or control traffic, account lockout mechanisms are used and continuous compliance audits are performed among other things. Since system hardening is a continuous dynamic process that is best implemented with a system hardening policy.
Most organizations follow a strict guideline based on system hardening standards such as CIS, NIST, ENISA, etc. To comply with popular security standards in the industry and to prevent cyberattacks, organizations must consistently undergo a system hardening process. System hardening works with the principle of defence-in-depth that enables organizations to build multiple layers of security to reduce the attack surface without compromising on the features and functionality of the applications and operating systems.
Broadly, system hardening is classified into the following types:
- Server hardening : To protect the ports, functions, data, and permissions on a server. Techniques include regularly updating/patching server software and strong passwords.
- Software hardening : To update security measures on all applications by editing/updating application code and prevent attacks.
- Operating system hardening : To make OS running on all endpoints secure. Techniques include updating patches and limiting accounts with access to the OS.
- Database hardening : To make the database and the DBMS secure. Techniques include limiting user privileges and access, disabling unnecessary services, and encrypting database information.
- Network hardening : To make all communication channels in the network between servers and endpoints secure.
Importance of System Hardening
System hardening ensures that the risk of cyberattacks on organizations is greatly minimized. One of the major reasons that result in audit issues and security breaches is configuration changes that result in compliance drifts. Every time a new server or user is added, or a new application is installed, it creates an opportunity for vulnerabilities to arise.
When organizations have numerous assets in the fleet with multiple configuration options, bringing every asset, old and new, in line with CIS benchmarks can take a long time with manual effort and introduce newer errors. Since these events are inevitable within the IT ecosystem, great care should be taken to ensure secure configuration and continuous compliance of the dynamic and ever-changing IT infrastructure. This can only be achieved by implementing automation tools that help in system hardening by continuously monitoring and auditing the organization’s heterogeneous IT assets and remediating drifts as and when they arise.
System Hardening Standards & Best Practices
System hardening is an essential process throughout the lifecycle of technology and is a requirement mentioned in mandates such as PCI DSS and HIPAA. The National Institute of Standards and Technology (NIST) and Center for Internet Security (CIS) maintain standards for system hardening best practices. The Special Publication (SP) 800-123 by NIST mentions some best system hardening practices, including establishing a thorough system security plan, regularly patching and updating OS, implementing encryption, etc. Similarly, CIS' Free Benchmarks offers useful tips to harden systems across the fleet.
A comprehensive system hardening strategy must include:
- A system hardening standard (CIS, NIST, ENISA, etc.) to follow.
- System hardening plan based on your organization's needs.
- System audits: Use a CIS benchmark-based security auditing tool to perform continuous audits and identify vulnerabilities in the systems.
- Quick vulnerability patching: Use an automation-based vulnerability scanning and patching tool to identify missing patches, security updates, and misconfigurations.
- Robust user permissions/access rules: Remove unnecessary accounts and privileges across the infrastructure.
- A CIS certified compliance automation solution with compliance reporting and automatic drift remediation.
System Hardening with Chef Compliance
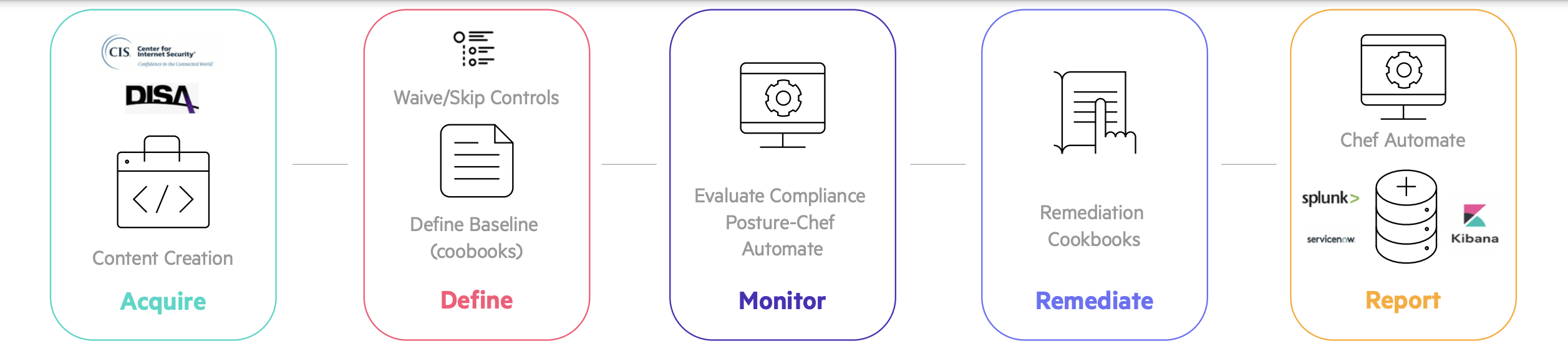
Chef Compliance is an automation solution that includes CIS and DISA STIG benchmarks to audit and remediate vulnerabilities in systems and help make IT ecosystems compliant and secure. With Chef Compliance, organizations can:
- Perform audits to assess the current state of configurations across heterogeneous estates
- Correct misconfigurations based on recommended CIS benchmarks and STIG
- Use exceptions and waivers in the audit process for specific controls
- Customize existing remediation content to suit organizations needs
- Rollback changes to the last known trusted state if a benchmark is compromised
- View the configuration status and compliance postures of all endpoints from a single dashboard
With Chef Compliance, enterprises can maintain security across hybrid and multi-cloud environments while also improving processes' overall efficiency and speed. Chef enables IT teams to perform system hardening with the help of continuous security audits and remediation that detects and fixes vulnerabilities in diverse IT fleets. The baselines are easily tuneable to organizational requirements, admins have total visibility, and the compliance profiles are easy to maintain even for massively distributed infrastructures.
Benefits of System Hardening with Chef
While there are numerous benefits of system hardening from security and compliance perspectives, the primary benefits are categorized as:
- Improved security postures: Continuous audits and remediation based on CIS and STIG standard profiles. This means all vulnerabilities are detected and addressed, ensuring reduced risk of data breaches, malware, and unauthorized access.
- Better auditability: Easy-to-read code that works across all platforms and Operating systems. Chef's curated profiles make complex security audits easier, fast, and more transparent.
- Improved system functionality: With error-free automation, speed of processes, consistency of configurations, and fully secure infrastructure, Chef improves the overall efficiency of all systems in the fleet and the productivity of the workforce.
If you are looking for an automation tool for your system hardening plans and to ensure compliance across heterogenous IT estates, Chef Compliance might be the tool for you. A CIS security software certification awarded solution, Chef allows IT teams to harden diverse systems with ease by taking care of configuration, security, and compliance automation within IT ecosystems. Try Chef Compliance today.
To know more about Chef Compliance and System Hardening, download our recent whitepaper titled 'Harden your systems using CIS and DISA STIGs benchmarks'.